netskope nsk300 practice test
Netskope Certified Cloud Security Architect
Question 1
You are asked to create a customized restricted administrator role in your Netskope tenant for a
newly hired employee. Which two statements are correct in this scenario? (Choose two.)
- A. An admin role prevents admins from downloading and viewing file content by default.
- B. The scope of the data shown in the Ul can be restricted to specific events.
- C. All role privileges default to Read Only for all functional areas.
- D. Obfuscation can be applied to all functional areas.
Answer:
AC
Explanation:
Admin Role and File Content Viewing: By default, an admin role does not prevent admins from
downloading and viewing file content. Admins have access to view and download file content unless
specific restrictions are applied.
Role Privileges Default to Read Only: All role privileges in Netskope default to Read Only for all
functional areas. This means that admins can view information but cannot make changes unless
explicitly granted additional permissions.
Obfuscation: Obfuscation can be applied to specific functional areas, but it is not a default behavior
for all areas. Reference:
Netskope Security Cloud Introductory Online Technical Training
Netskope Security Cloud Operation & Administration (NSCO&A) - Classroom Training
Question 2
You are deploying the Netskope Client to Windows devices. The following command line would be
used to install the client MSI file: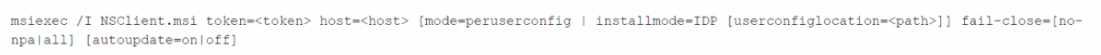
In this scenario, what is <token> referring to in the command line?
- A. a Netskope user identifier
- B. the Netskope organization ID
- C. the URL of the IdP used to authenticate the users
- D. a private token given to you by the SCCM administrator
Answer:
B
Explanation:
In the context of deploying the Netskope Client to Windows devices, <token> in the command line
refers to the Netskope organization ID. This is a unique identifier associated with your organization’s
account within the Netskope security cloud. It is used during the installation process to ensure that
client devices are registered and managed under the correct organizational account, enabling
appropriate security policies and configurations to be applied. Reference: The answer can be inferred
from general knowledge about installing software clients and isn’t directly available on Netskope’s
official resources.
Question 3
Given the following:
Which result does this Skope IT query provide?
- A. The query returns all events of [email protected] downloading or uploading to or from the site 'Amazon S3" using the Netskope Client.
- B. The query returns all events of an IP address downloading or uploading to or from Amazon S3 using the Netskope Client.
- C. The query returns all events of everyone except [email protected] downloading or uploading to or from the site "Amazon S3" using the Netskope Client.
- D. The query returns all events of [email protected] downloading or uploading to or from the application "Amazon S3" using the Netskope Client.
Answer:
A
Explanation:
The given Skope IT query specifies the following conditions:
User equals ‘[email protected]’
Access method equals ‘Client’
Activity equals ‘Download’ or ‘Upload’
Site equals ‘Amazon S3’
The query combines these conditions using logical operators (AND and OR).
The result of this query will include all events where the specified user (‘[email protected]’) is
either downloading or uploading data to or from the site ‘Amazon S3’ using the Netskope Client.
It does not include events related to other users or IP addresses. Reference:
Netskope Security Cloud Introductory Online Technical Training
Netskope Security Cloud Operation & Administration (NSCO&A) - Classroom Training
Question 4
You want customers to configure Real-time Protection policies. In which order should the policies be
placed in this scenario?
- A. Threat, CASB, RBI, Web
- B. RBI, CASB, Web, Threat
- C. Threat, RBI, CASB, Web
- D. CASB, RBI, Threat, Web
Answer:
B
Explanation:
When configuring Real-time Protection policies in Netskope, the recommended order is as follows:
RBI (Risk-Based Index) Policies: These policies focus on risk assessment and prioritize actions based
on risk scores. They help identify high-risk activities and users.
CASB (Cloud Access Security Broker) Policies: These policies address cloud-specific security
requirements, such as controlling access to cloud applications, enforcing data loss prevention (DLP)
rules, and managing shadow IT.
Web Policies: These policies deal with web traffic, including URL filtering, web categories, and threat
prevention.
Threat Policies: These policies focus on detecting and preventing threats, such as malware, phishing,
and malicious URLs.
Placing the policies in this order ensures that risk assessment and cloud-specific controls are applied
before addressing web and threat-related issues. Reference:
Netskope Security Cloud Introductory Online Technical Training
Netskope Security Cloud Operation & Administration (NSCO&A) - Classroom Training
Netskope Certification Description
Netskope Architectural Advantage Features
Question 5
A company has deployed Explicit Proxy over Tunnel (EPoT) for their VDI users They have configured
Forward Proxy authentication using Okta Universal Directory They have also configured a number of
Real-time Protection policies that block access to different Web categories for different AD groups so.
for example, marketing users are blocked from accessing gambling sites. During User Acceptance
Testing, they see inconsistent results where sometimes marketing users are able to access gambling
sites and sometimes they are blocked as expected They are seeing this inconsistency based on who
logs into the VDI server first.
What is causing this behavior?
- A. Forward Proxy is not configured to use the Cookie Surrogate
- B. Forward Proxy is not configured to use the IP Surrogate
- C. Forward Proxy authentication is configured but not enabled.
- D. Forward Proxy is configured to use the Cookie Surrogate
Answer:
A
Explanation:
The inconsistent results observed during User Acceptance Testing (where marketing users sometimes
access gambling sites and sometimes are blocked) are likely due to the configuration of the Forward
Proxy.
Cookie Surrogate: The Cookie Surrogate is a mechanism used in Forward Proxy deployments to
maintain user context across multiple requests. It ensures that user-specific policies are consistently
applied even when multiple users share the same IP address (common in VDI environments).
Issue: If the Forward Proxy is not configured to use the Cookie Surrogate, it may lead to inconsistent
behavior. When different users log into the VDI server, their requests may not be associated with
their specific user context, resulting in varying policy enforcement.
Solution: Ensure that the Forward Proxy is properly configured to use the Cookie Surrogate, allowing
consistent policy enforcement based on individual user identities. Reference:
Netskope Security Cloud Operation & Administration (NSCO&A) - Classroom Training
Netskope Security Cloud Introductory Online Technical Training
Netskope Architectural Advantage Features
Question 6
Review the exhibit.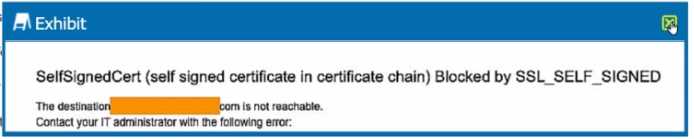
You are the proxy administrator for a medical devices company. You recently changed a pilot group of
users from cloud app steering to all Web traffic. Pilot group users have started to report that they
receive the error shown in the exhibit when attempting to access the company intranet site that is
publicly available. During troubleshooting, you realize that this site uses your company's internal
certificate authority for SSL certificates.
Which three statements describe ways to solve this issue? (Choose three.)
- A. Import the root certificate for your internal certificate authority into Netskope.
- B. Bypass SSL inspection for the affected site(s).
- C. Create a Real-time Protection policy to allow access.
- D. Change the SSL Error Settings from Block to Bypass in the Netskope tenant.
- E. Instruct the user to proceed past the error message
Answer:
ABD
Explanation:
A . Import the root certificate for your internal certificate authority into Netskope:
This step ensures that Netskope recognizes and trusts SSL certificates issued by your company’s
internal certificate authority. By importing the root certificate, you enable proper SSL inspection and
validation for internal sites.
B . Bypass SSL inspection for the affected site(s):
Since the intranet site uses your company’s internal certificate authority, bypassing SSL inspection for
this specific site allows users to access it without encountering SSL errors.
D . Change the SSL Error Settings from Block to Bypass in the Netskope tenant:
Adjusting the SSL Error Settings to “Bypass” allows users to proceed past SSL errors, including self-
signed certificate errors. This ensures uninterrupted access to the intranet site. Reference:
Netskope Security Cloud Introductory Online Technical Training
Netskope Security Cloud Operation & Administration (NSCO&A) - Classroom Training
Netskope Cloud Security Certification Program
Question 7
Review the exhibit.
You created an SSL decryption policy to bypass the inspection of financial and accounting Web
categories. However, you still see banking websites being inspected.
Referring to the exhibit, what are two possible causes of this behavior? (Choose two.)
- A. The policy is in a "disabled" state.
- B. An incorrect category has been selected
- C. The policy is in a "pending changes" state.
- D. An incorrect action has been specified.
Answer:
B, D
Explanation:
The issue described in the exhibit is that banking websites are still being inspected despite creating
an SSL decryption policy to bypass the inspection of financial and accounting web categories.
Possible Causes:
An incorrect category has been selected (Option B):
If the SSL decryption policy is configured to bypass the wrong category (e.g., not the actual financial
and accounting category), it won’t effectively exclude banking websites from inspection.
An incorrect action has been specified (Option D):
If the action specified in the policy is not set to “Bypass,” it won’t achieve the desired behavior. The
policy should explicitly bypass SSL inspection for the selected category.
Solution:
Verify that the correct category (financial and accounting) is selected in the policy, and ensure that
the action is set to “Bypass.”
Question 8
You deployed the Netskope Client for Web steering in a large enterprise with dynamic steering. The
steering configuration includes a bypass rule for an application that is IP restricted. What is the
source IP for traffic to this application when the user is on-premises at the enterprise?
- A. Loopback IPv4
- B. Netskope data plane gateway IPv4
- C. Enterprise Egress IPv4
- D. DHCP assigned RFC1918 IPv4
Answer:
C
Explanation:
When a user is on-premises at the enterprise and accesses an application that is IP restricted, the
source IP for traffic to this application is the Enterprise Egress IPv4 address.
The Enterprise Egress IP represents the external IP address of the enterprise network as seen by
external services or applications.
This IP address is used for communication between the user’s device and external resources,
including applications that are IP restricted. Reference:
The answer is based on general knowledge of networking concepts and how IP addresses are used in
enterprise environments.
Question 9
You do not want a scheduled Advanced Analytics dashboard to be automatically updated when
Netskope makes improvements to that dashboard. In this scenario, what would you do to retain the
original dashboard?
- A. Create a new dashboard from scratch that mimics the Netskope dashboard you want to use.
- B. Copy the dashboard into your Group or Personal folders and schedule from these folders.
- C. Ask Netskope Support to provide the dashboard and import into your Personal folder.
- D. Download the dashboard you want and Import from File into your Group or Personal folder.
Answer:
D
Explanation:
To retain the original dashboard without automatic updates due to improvements made by
Netskope, you can download the desired dashboard and then import it from a file into your Group or
Personal folder.
This approach ensures that you have a static version of the dashboard that won’t be affected by
future changes or enhancements. Reference:
The answer is based on general knowledge of dashboard management and customization within
Netskope.
Question 10
You have multiple networking clients running on an endpoint and client connectivity is a concern.
You are configuring co-existence with a VPN solution in this scenario, what is recommended to
prevent potential routing issues?
- A. Configure the VPN to split tunnel traffic by adding the Netskope IP and Google DNS ranges and set to Exclude in the VPN configuration.
- B. Modify the VPN to operate in full tunnel mode at Layer 3. so that the Netskope agent will always see the traffic first.
- C. Configure the VPN to full tunnel traffic and add an SSL Do Not Decrypt policy to the VPN configuration for all Netskope traffic.
- D. Configure a Network Location with the VPN IP ranges and add it as a Steering Configuration exception.
Answer:
B
Explanation:
To prevent potential routing issues and ensure that the Netskope agent consistently sees the traffic
first, it is recommended to modify the VPN to operate in full tunnel mode at Layer 3.
In full tunnel mode, all traffic from the endpoint is routed through the VPN, including traffic destined
for Netskope. This ensures that the Netskope agent can inspect and apply policies to all traffic,
regardless of the destination.
Layer 3 full tunnel mode provides better visibility and control over the traffic flow, reducing the risk
of routing conflicts or bypassing the Netskope inspection. Reference:
The answer is based on general knowledge of VPN configurations and their impact on traffic routing.
Question 11
Review the exhibit.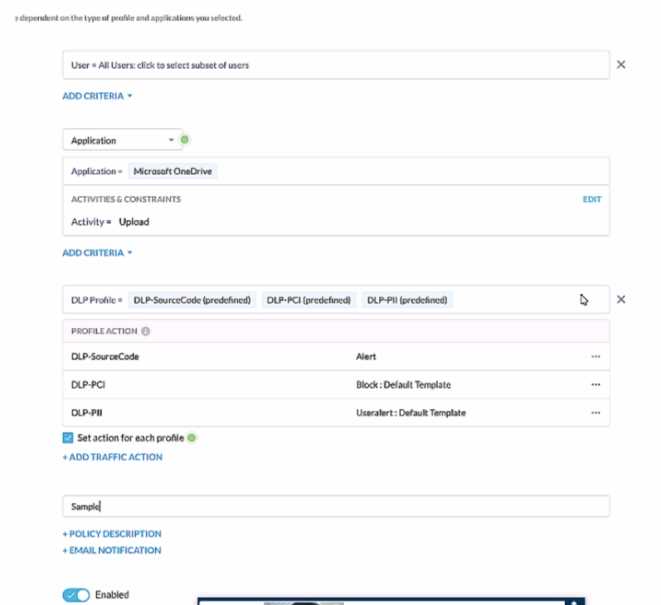
A user has attempted to upload a file to Microsoft OneDrive that contains source code with Pll and
PCI data.
Referring to the exhibit, which statement Is correct?
- A. The user will be blocked and a single Incident will be generated referencing the DLP-PCI profile.
- B. The user will be blocked and a single Incident will be generated referencing all of the matching DLP profiles
- C. The user will be blocked and a separate incident will be generated for each of the matching DLP profiles.
- D. The user will be alerted and a single incident will be generated referencing the DLP-PII profile.
Answer:
C
Explanation:
In the given scenario, a user is attempting to upload a file containing sensitive PII and PCI data to
Microsoft OneDrive. The Netskope Security Cloud provides real-time data and threat protection
when accessing cloud services, websites, and private apps from anywhere, on any device. Based on
the exhibit provided, different DLP (Data Loss Prevention) profiles are triggered - DLP-SourceCode,
DLP-PCI, and DLP-PII. Each of these profiles has specific actions associated with them; for instance, an
alert is generated for Source Code while blocking actions are initiated for PCI and PII data. Since
multiple DLP profiles are triggered due to the sensitive nature of the content in the file being
uploaded, separate incidents will be generated for each matching profile ensuring comprehensive
security coverage and incident reporting.
Reference:
Netskope Cloud Security
Netskope Resources
Netskope Documentation
Question 12
Users at your company's branch office in San Francisco report that their clients are connecting, but
websites and SaaS applications are slow When troubleshooting, you notice that the users are
connected to a Netskope data plane in New York where your company's headquarters is located.
What is a valid reason for this behavior?
- A. The Netskope Client's on-premises detection check failed.
- B. The Netskope Client's default DNS over HTTPS call is failing.
- C. The closest Netskope data plane to San Francisco is unavailable.
- D. The Netskope Client's DNS call to Secure Forwarder is failing
Answer:
C
Explanation:
The reported issue of slow website and SaaS application access for users in the San Francisco branch
office, despite being connected to a Netskope data plane in New York, can be attributed to the
geographical distance between the user location and the data plane. The Netskope Security Cloud
operates through a distributed network of data planes strategically placed in various regions. When
users connect to a data plane that is geographically distant, it can result in latency due to longer
network traversal times. In this case, the closest Netskope data plane to San Francisco might be
unavailable or experiencing high load, leading to performance issues. To address this, consider
optimizing data plane selection based on proximity to the user location or investigating any data
plane availability or performance issues.
Reference:
Netskope Cloud Security
Netskope Resources
Netskope Documentation
Question 13
You need to extract events and alerts from the Netskope Security Cloud platform and push it to a
SIEM solution. What are two supported methods to accomplish this task? (Choose two.)
- A. Use Cloud Ticket Orchestrator.
- B. Use Cloud Log Shipper.
- C. Stream directly to syslog.
- D. Use the REST API.
Answer:
B, D
Explanation:
To extract events and alerts from the Netskope Security Cloud platform and integrate them with a
SIEM (Security Information and Event Management) solution, you can utilize the following supported
methods:
Cloud Log Shipper (CLS):
The Cloud Log Shipper is designed to forward Netskope logs to external systems, including SIEMs.
It allows you to export logs in real-time or batch mode to a destination of your choice.
By configuring CLS, you can ensure that Netskope events and alerts are sent to your SIEM for further
analysis and correlation.
Reference: Netskope Documentation on Cloud Log Shipper
REST API:
The Netskope Security Cloud provides a comprehensive REST API that allows you to
programmatically retrieve data, including events and alerts.
You can use the REST API to query specific logs, incidents, or other relevant information from
Netskope.
By integrating with the REST API, you can extract data and push it to your SIEM solution.
Reference: Netskope REST API Documentation
Reference:
Netskope Cloud Security
Netskope Resources
Netskope Documentation
These methods ensure seamless data flow between Netskope and your SIEM, enabling effective
security monitoring and incident response.
Question 14
You want to enable the Netskope Client to automatically determine whether it is on-premises or off-
premises. Which two options in the Netskope Ul would you use to accomplish this task? (Choose
two.)
- A. the All Traffic option in the Steering Configuration section of the Ul
- B. the New Exception option in the Traffic Steering options of the Ul
- C. the Enable Dynamic Steering option in the Steering Configuration section of the Ul
- D. the On Premises Detection option under the Client Configuration section of the Ul
Answer:
C, D
Explanation:
To enable the Netskope Client to automatically determine whether it is on-premises or off-premises,
you can use the following options in the Netskope UI:
Enable Dynamic Steering:
This option is available in the Steering Configuration section of the UI.
By enabling dynamic steering, the Netskope Client can intelligently determine the appropriate data
plane (on-premises or cloud) based on the user’s location and network conditions.
It ensures that traffic is directed to the optimal data plane for improved performance and security.
Reference: Netskope Documentation on Dynamic Steering
On Premises Detection:
This option is available under the Client Configuration section of the UI.
By configuring on-premises detection, the Netskope Client can identify whether it is connected to
the local network (on-premises) or accessing resources from outside (off-premises).
It helps in applying relevant policies and steering traffic accordingly.
Reference: Netskope Documentation on Client Configuration
Question 15
You are already using Netskope CSPM to monitor your AWS accounts for compliance. Now you need
to allow access from your company-managed devices running the Netskope Client to only Amazon S3
buckets owned by your organization. You must ensure that any current buckets and those created in
the future will be allowed
Which configuration satisfies these requirements?
- A. Steering: Cloud Apps Only, All Traffic Policy type: Real-time Protection Constraint: Storage. Bucket Does Not Match -ALLAccounts Action: Block
- B. Steering: Cloud Apps Only Policy type: Real-time Protection Constraint: Storage. Bucket Does Not Match *@myorganization.com Action: Block
- C. Steering: Cloud Apps Only. All Traffic Policy type: Real-time Protection Constraint: Storage. Bucket Does Match -ALLAccounts Action: Allow
- D. Steering: All Web Traffic Policy type: API Data Protection Constraint: Storage, Bucket Does Match *@myorganization.com Action: Allow
Answer:
C
Explanation:
To allow access from company-managed devices running the Netskope Client to only Amazon S3
buckets owned by the organization, the following configuration satisfies the requirements:
Steering Configuration:
Policy Type: Real-time Protection
Constraint: Storage
Bucket Condition: Bucket Does Match -ALLAccounts
Action: Allow
By configuring the policy to allow traffic from company-managed devices (Netskope Clients) to
Amazon S3 buckets, the organization ensures that only buckets owned by the organization are
accessible.
The -ALLAccounts condition ensures that both existing and future buckets are allowed.
This configuration aligns with the requirement to allow access to organization-owned buckets while
blocking access to other buckets.
Reference:
Netskope Cloud Security
Netskope Solution Brief
Netskope Community