microsoft az-220 practice test
Microsoft Azure IoT Developer
Note: Test Case questions are at the end of the exam
Question 1 Topic 1, Case Study 1Case Study Question View Case
What should you do to identify the cause of the connectivity issues?
- A. Send cloud-to-device messages to the IoT devices.
- B. Use the heartbeat pattern to send messages from the IoT devices to iothub1.
- C. Monitor the connection status of the device twin by using an Azure function.
- D. Enable the collection of the Connections diagnostic logs and set up alerts for the connected devices count metric.
Answer:
D
Explanation:
Scenario: You discover connectivity issues between the IoT gateway devices and iothub1, which cause IoT devices to lose
connectivity and messages.
To log device connection events and errors, turn on diagnostics for IoT Hub. We recommend turning on these logs as early
as possible, because if diagnostic logs aren't enabled, when device disconnects occur, you won't have any information to
troubleshoot the problem with.
Step 1:
1. Sign in to the Azure portal.
2. Browse to your IoT hub.
3. Select Diagnostics settings.
4. Select Turn on diagnostics.
5. Enable Connections logs to be collected.
6. For easier analysis, turn on Send to Log Analytics (see pricing).
Step 2:
Set up alerts for device disconnect at scale
To get alerts when devices disconnect, configure alerts on the Connected devices (preview) metric.
Reference: https://docs.microsoft.com/bs-cyrl-ba/azure/iot-hub/iot-hub-troubleshoot-connectivity
Question 2 Topic 1, Case Study 1Case Study Question View Case
HOTSPOT
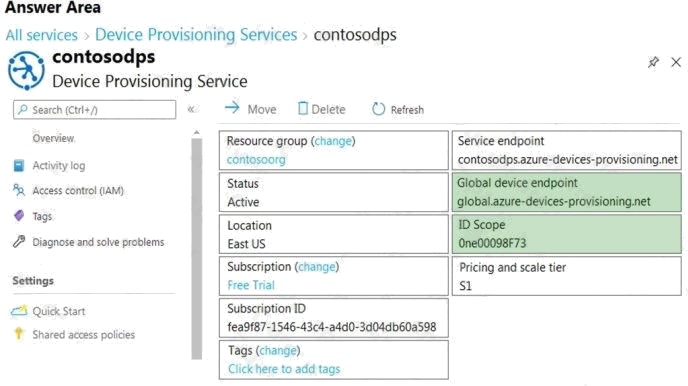
You are writing code to provision IoT devices by using the Device Provisioning Service.
Which two details from the Overview blade of the Device Provisioning Service are required to provision a new IoT client
device? To answer, select the appropriate detail in the answer area.
NOTE: Each correct selection is worth one point.
Hot Area: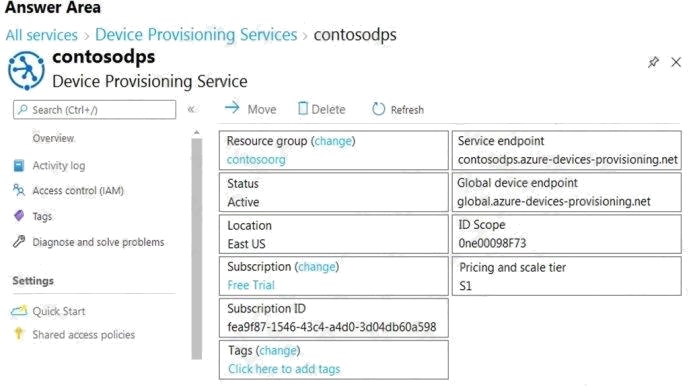
Answer:
Explanation:
Box 1: ID Scope
In the Azure portal, select the Overview blade for your Device Provisioning service and copy the ID Scope value. The ID
Scope is generated by the service and guarantees uniqueness. It is immutable and used to uniquely identify the registration
IDs.
Box 2: Global device endpoint
The global_prov_uri variable, which allows the IoT Hub client registration API IoTHubClient_LL_CreateFromDeviceAuth to
connect with the designated Device Provisioning Service instance.
Example code:
static const char* global_prov_uri = "global.azure-devices-provisioning.net"; static const char* id_scope = "[ID Scope]";
Reference:
https://docs.microsoft.com/en-us/azure/iot-dps/tutorial-set-up-device
Provision and manage devices
Question 3 Topic 2, Case Study 2Case Study Question View Case
You plan to deploy Azure Time Series Insights.
What should you create on iothub1 before you deploy Time Series Insights?
- A. a new message route
- B. a new consumer group
- C. a new shared access policy
- D. an IP filter rule
Answer:
B
Explanation:
Create a dedicated consumer group in the IoT hub for the Time Series Insights environment to consume from. Each Time
Series Insights event source must have its own dedicated consumer group that isn't shared with any other consumer. If
multiple readers consume events from the same consumer group, all readers are likely to exhibit failures. Reference:
https://docs.microsoft.com/en-us/azure/time-series-insights/time-series-insights-how-to-add-an-event-source-iothub
Question 4 Topic 2, Case Study 2Case Study Question View Case
How should you complete the GROUP BY clause to meet the Streaming Analytics requirements?
- A. GROUP BY HoppingWindow(Second, 60, 30)
- B. GROUP BY TumblingWindow(Second, 30)
- C. GROUP BY SlidingWindow(Second, 30)
- D. GROUP BY SessionWindow(Second, 30, 60)
Answer:
B
Explanation:
Scenario: You plan to use a 30-second period to calculate the average temperature reading of the sensors.
Tumbling window functions are used to segment a data stream into distinct time segments and perform a function against
them, such as the example below. The key differentiators of a Tumbling window are that they repeat, do not overlap, and an
event cannot belong to more than one tumbling window.
Incorrect Answers:
A: Hopping window functions hop forward in time by a fixed period. It may be easy to think of them as Tumbling windows that
can overlap, so events can belong to more than one Hopping window result set. Reference:
https://docs.microsoft.com/en-us/azure/stream-analytics/stream-analytics-window-functions
Question 5 Topic 2, Case Study 2Case Study Question View Case
HOTSPOT
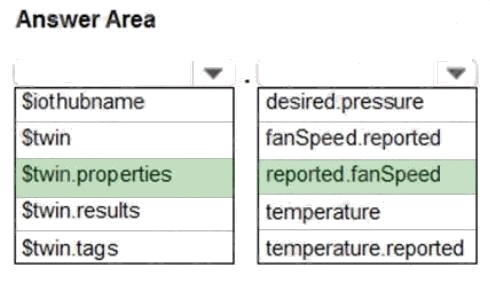
You need to use message enrichment to add additional device information to messages sent from the IoT gateway devices
when the reported temperature exceeds a critical threshold.
How should you configure the enrich message values? To answer, select the appropriate options in the answer area.
NOTE: Each correct selection is worth one point.
Hot Area: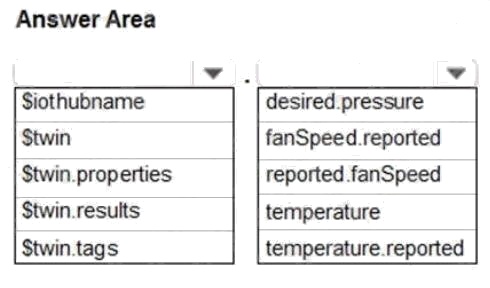
Answer:
Explanation:
Reference: https://docs.microsoft.com/bs-cyrl-ba/azure/iot-hub/iot-hub-message-enrichments-overview
Process and manage data
Question 6 Topic 3, Case Study 3Case Study Question View Case
You need to configure Stream Analytics to meet the POV requirements.
What are two ways to achieve the goal? Each correct answer presents a complete solution.
NOTE: Each correct selection is worth one point.
- A. From IoT Hub, create a custom event hub endpoint, and then configure the endpoint as an input to Stream Analytics.
- B. Create a Stream Analytics module, and then deploy the module to all IoT Edge devices in the fleet.
- C. Create an input in Stream Analytics that uses the built-in events endpoint of IoT Hub as the source.
- D. Route telemetry to an Azure Blob storage custom endpoint, and then configure the Blob storage as a reference input for Stream Analytics.
Answer:
A C
Question 7 Topic 3, Case Study 3Case Study Question View Case
DRAG DROP
You need to add Time Series Insights to the solution to meet the pilot requirements.
Which three actions should you perform in sequence? To answer, move the appropriate actions from the list of actions to the
answer area and arrange them in the correct order.
Select and Place: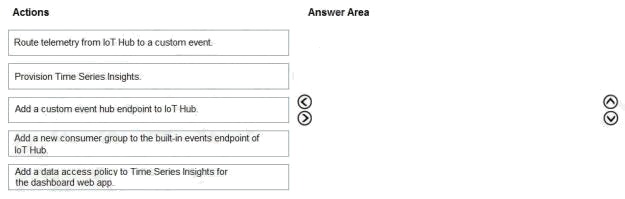
Answer:
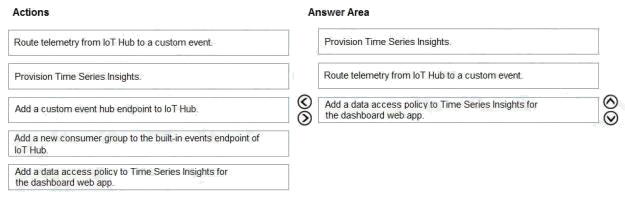
Explanation:
Step 1: Provision Time Series Insights
Select Provision new IoT Hub to create a new IoT hub.
Step 2: Route telemetry from IoT Hub to a custom event.
Step 3: Add a data access policy to Time Series Insights for the dashboard web app
Scenario: Requirements. Pilot Requirements
During the pilot phase, devices will be deployed to 10 offices. Each office will have up to 1,000 devices.
During this phase, you will add Azure Time Series Insights in parallel to Stream Analytics to support real-time graphs and
queries in a dashboard web app.
The pilot deployment must minimize operating costs.
Incorrect Answers:
No need to use an endpoint.
Reference: https://docs.microsoft.com/en-us/azure/time-series-insights/time-series-insights-update-create-environment
Question 8 Topic 3, Case Study 3Case Study Question View Case
You need to store the real-time alerts generated by Stream Analytics to meet the technical requirements.
Which type of Stream Analytics output should you configure?
- A. Azure Blob storage
- B. Microsoft Power BI
- C. Azure Cosmos DB
- D. Azure SQL Database
Answer:
A
Explanation:
When you create a Time Series Insights Preview pay-as-you-go (PAYG) SKU environment, you create two Azure resources:
An Azure Storage general-purpose V1 blob account for cold data storage.
An Azure Time Series Insights Preview environment that can be configured for warm data storage. Reference:
https://docs.microsoft.com/en-us/azure/time-series-insights/time-series-insights-update-storage-ingress
Question 9 Topic 3, Case Study 3Case Study Question View Case
You need to recommend the format of telemetry messages to meet the POV requirements.
What should you recommend?
- A. XML
- B. Avro
- C. JSON
Answer:
C
Explanation:
Scenario: POV Requirements
Ensure that all message content during this phase is human readable to simplify debugging.
Avro uses a binary format, so it is not human readable.
The more lightweight JSON (Javascript object notation) has become a popular alternative to XML for various reasons. A
couple obvious ones are:
Less verbose- XML uses more words than necessary
JSON is faster- Parsing XML software is slow and cumbersome. Reference:
https://blog.cloud-elements.com/json-better-xml
Question 10 Topic 3, Case Study 3Case Study Question View Case
During the POV phase, telemetry from IoT Hub stops flowing to the hot path. The cold path continues to work.
What should you do to restore the hot path?
- A. Disable the fallback route.
- B. Run the Test all routes action.
- C. Create an explicit route for the hot path.
- D. Modify cold-route to send only some telemetry data to the cold path.
Answer:
C
Question 11 Topic 4, Mixed Questions
HOTSPOT
You create a new IoT device named device1 on iothub1. Device1 has a primary key of Uihuih76hbHb.
How should you complete the device connection string? To answer, select the appropriate options in the answer area.
NOTE: Each correct selection is worth one point.
Hot Area: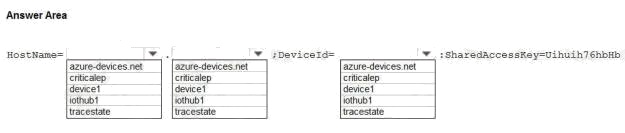
Answer:
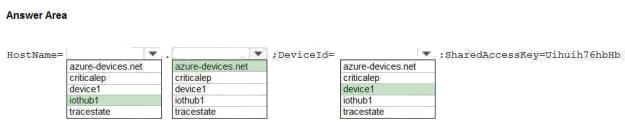
Explanation:
Box 1: iothub1
The Azure IoT hub is named iothub1.
Box 2: azure-devices.net
The format of the device connection string looks like:
HostName={YourIoTHubName}.azure-devices.net;DeviceId=MyNodeDevice;SharedAccessKey={YourSharedAccessKey}
Box 1: device1
Device1 has a primary key of Uihuih76hbHb.
Reference:
https://docs.microsoft.com/en-us/azure/iot-hub/quickstart-control-device-dotnet
Implement the IoT solution infrastructure
Question 12 Topic 4, Mixed Questions
Note: This question is part of a series of questions that present the same scenario. Each question in the series contains a
unique solution that might meet the stated goals. Some question sets might have more than one correct solution, while
others might not have a correct solution.
After you answer a question in this section, you will NOT be able to return to it. As a result, these questions will not appear in
the review screen.
You have an Azure IoT solution that includes an Azure IoT hub, a Device Provisioning Service instance, and 1,000
connected IoT devices.
All the IoT devices are provisioned automatically by using one enrollment group.
You need to temporarily disable the IoT devices from the connecting to the IoT hub.
Solution: From the Device Provisioning Service, you disable the enrollment group, and you disable device entries in the
identity registry of the IoT hub to which the IoT devices are provisioned.
Does the solution meet the goal?
- A. Yes
- B. No
Answer:
A
Explanation:
You may find it necessary to deprovision devices that were previously auto-provisioned through the Device Provisioning
Service.
In general, deprovisioning a device involves two steps:
1. Disenroll the device from your provisioning service, to prevent future auto-provisioning. Depending on whether you want to
revoke access temporarily or permanently, you may want to either disable ordelete an enrollment entry.
2. Deregister the device from your IoT Hub, to prevent future communications and data transfer. Again, you can temporarily
disable or permanently delete the device's entry in the identity registry for the IoTHub where it was provisioned.
Reference: https://docs.microsoft.com/bs-latn-ba/azure/iot-dps/how-to-unprovision-devices
Question 13 Topic 4, Mixed Questions
Note: This question is part of a series of questions that present the same scenario. Each question in the series contains a
unique solution that might meet the stated goals. Some question sets might have more than one correct solution, while
others might not have a correct solution.
After you answer a question in this section, you will NOT be able to return to it. As a result, these questions will not appear in
the review screen.
You have an Azure IoT solution that includes an Azure IoT hub, a Device Provisioning Service instance, and 1,000
connected IoT devices.
All the IoT devices are provisioned automatically by using one enrollment group.
You need to temporarily disable the IoT devices from the connecting to the IoT hub.
Solution: You delete the enrollment group from the Device Provisioning Service.
Does the solution meet the goal?
- A. Yes
- B. No
Answer:
B
Explanation:
Instead, from the Device Provisioning Service, you disable the enrollment group, and you disable device entries in the
identity registry of the IoT hub to which the IoT devices are provisioned.
Reference: https://docs.microsoft.com/bs-latn-ba/azure/iot-dps/how-to-unprovision-devices
Question 14 Topic 4, Mixed Questions
Note: This question is part of a series of questions that present the same scenario. Each question in the series contains a
unique solution that might meet the stated goals. Some question sets might have more than one correct solution, while
others might not have a correct solution.
After you answer a question in this section, you will NOT be able to return to it. As a result, these questions will not appear in
the review screen.
You have an Azure IoT solution that includes an Azure IoT hub, a Device Provisioning Service instance, and 1,000
connected IoT devices.
All the IoT devices are provisioned automatically by using one enrollment group.
You need to temporarily disable the IoT devices from the connecting to the IoT hub.
Solution: From the IoT hub, you change the credentials for the shared access policy of the IoT devices.
Does the solution meet the goal?
- A. Yes
- B. No
Answer:
B
Explanation:
Reference: https://docs.microsoft.com/bs-latn-ba/azure/iot-dps/how-to-unprovision-devices
Question 15 Topic 4, Mixed Questions
HOTSPOT
You have an Azure IoT hub.
You plan to deploy 1,000 IoT devices by using automatic device management.
The device twin is shown below.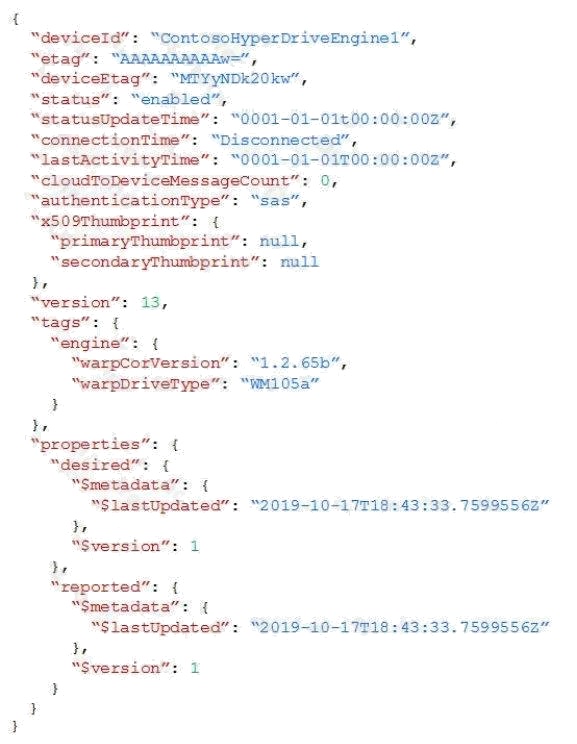
You need to configure automatic device management for the deployment.
Which target Condition and Device Twin Path should you use? To answer, select the appropriate options in the answer area.
NOTE: Each correct selection is worth one point.
Hot Area: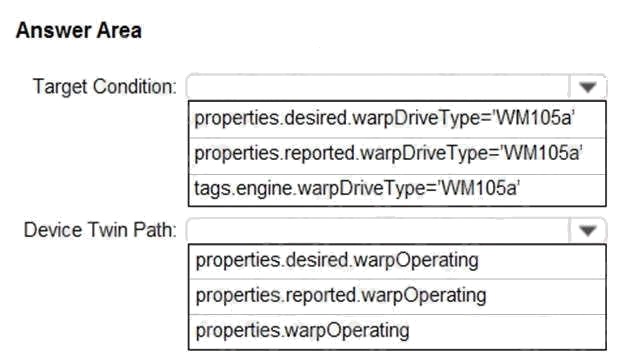
Answer:
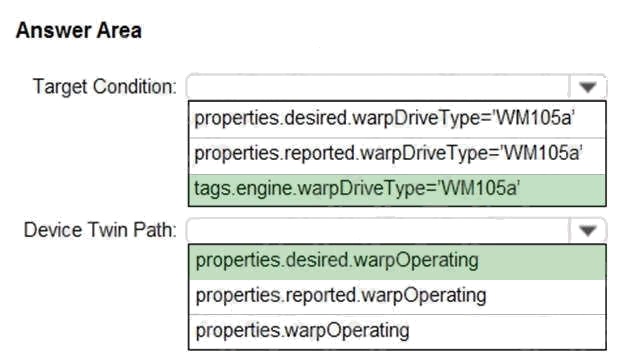
Explanation:
Box 1: tags.engine.warpDriveType='VM105a'
Use tags to target twins. Before you create a configuration, you must specify which devices or modules you want to affect.
Azure IoT Hub identifies devices and using tags in the device twin, and identifies modules using tags in the module twin.
Box 2: properties.desired.warpOperating
The twin path, which is the path to the JSON section within the twin desired properties that will be set.
For example, you could set the twin path to properties.desired.chiller-water and then provide the following JSON content:
{
"temperature": 66,
"pressure": 28
}
Reference: https://docs.microsoft.com/en-us/azure/iot-hub/iot-hub-automatic-device-management