Fortinet nse4-fgt-7-2 practice test
Fortinet NSE 4 - FortiOS 7.2
Question 1
Which two statements are correct about NGFW Policy-based mode? (Choose two.)
- A. NGFW policy-based mode does not require the use of central source NAT policy
- B. NGFW policy-based mode can only be applied globally and not on individual VDOMs
- C. NGFW policy-based mode supports creating applications and web filtering categories directly in a firewall policy
- D. NGFW policy-based mode policies support only flow inspection
Answer:
CD
Question 2
Refer to the exhibit.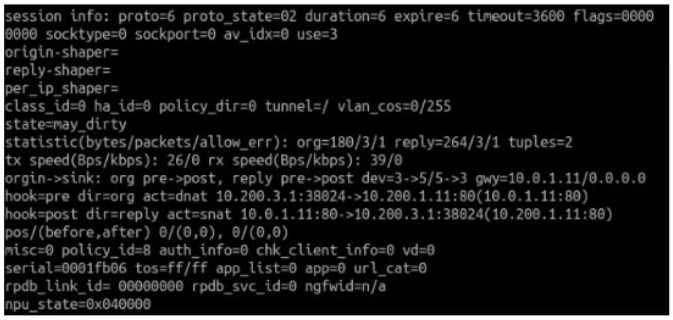
Which contains a session diagnostic output. Which statement is true about the session diagnostic
output?
- A. The session is in SYN_SENT state.
- B. The session is in FIN_ACK state.
- C. The session is in FTN_WAIT state.
- D. The session is in ESTABLISHED state.
Answer:
A
Explanation:
Indicates TCP (proto=6) session in SYN_SENT state (proto=state=2)
https://kb.fortinet.com/kb/viewContent.do?externalId=FD30042
Question 3
Which two statements explain antivirus scanning modes? (Choose two.)
- A. In proxy-based inspection mode, files bigger than the buffer size are scanned.
- B. In flow-based inspection mode, FortiGate buffers the file, but also simultaneously transmits it to the client.
- C. In proxy-based inspection mode, antivirus scanning buffers the whole file for scanning, before sending it to the client.
- D. In flow-based inspection mode, files bigger than the buffer size are scanned.
Answer:
BC
Explanation:
An antivirus profile in full scan mode buffers up to your specified file size limit. The default is 10 MB.
That is large enough for most files, except video files. If your FortiGate model has more RAM, you
may be able to increase this threshold. Without a limit, very large files could exhaust the scan
memory. So, this threshold balances risk and performance. Is this tradeoff unique to FortiGate, or
to a specific model? No. Regardless of vendor or model, you must make a choice. This is because of
the difference between scans in theory, that have no limits, and scans on real-world devices, that
have finite RAM. In order to detect 100% of malware regardless of file size, a firewall would need
infinitely large RAM--something that no device has in the real world. Most viruses are very small.
This table shows a typical tradeoff. You can see that with the default 10 MB threshold, only 0.01% of
viruses pass through.
FortiGate Security 7.2 Study Guide (p.350 & 352): "In flow-based inspection mode, the IPS engine
reads the payload of each packet, caches a local copy, and forwards the packet to the receiver at the
same time. Because the file is ransmitted simultaneously, flow-based mode consumes more CPU
cycles than proxy-based." "Each protocol’s proxy picks up a connection and buffers the entire file first
(or waits until the oversize limit is reached) before scanning. The client must wait for the scanning to
finish."
Question 4
Refer to the exhibit.
Refer to the web filter raw logs.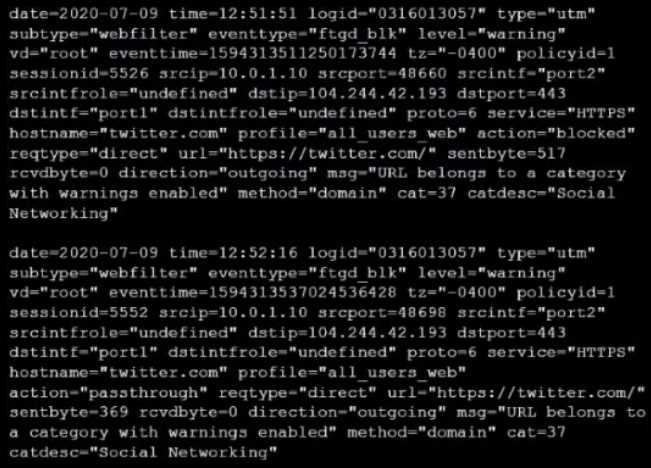
Based on the raw logs shown in the exhibit, which statement is correct?
- A. Social networking web filter category is configured with the action set to authenticate.
- B. The action on firewall policy ID 1 is set to warning.
- C. Access to the social networking web filter category was explicitly blocked to all users.
- D. The name of the firewall policy is all_users_web.
Answer:
A
Question 5
Which two configuration settings are synchronized when FortiGate devices are in an active-active HA
cluster? (Choose two.)
- A. FortiGuard web filter cache
- B. FortiGate hostname
- C. NTP
- D. DNS
Answer:
CD
Explanation:
In the 7.2 Infrastructure Guide (page 306) the list of configuration settings that are NOT synchronized
includes both 'FortiGate host name' and 'Cache'
Question 6
An administrator wants to configure timeouts for users. Regardless of the userTMs behavior, the
timer should start as soon as the user authenticates and expire after the configured value.
Which timeout option should be configured on FortiGate?
- A. auth-on-demand
- B. soft-timeout
- C. idle-timeout
- D. new-session
- E. hard-timeout
Answer:
E
Explanation:
https://community.fortinet.com/t5/FortiGate/Technical-Tip-Explanation-of-auth-timeout-types-for-
Firewall/ta-p/189423
Reference:
https://kb.fortinet.com/kb/documentLink.do?externalID=FD37221#:~:text=Hard%20timeout%3A%2
0User%20
Question 7
Why does FortiGate Keep TCP sessions in the session table for several seconds, even after both sides
(client and server) have terminated the session?
- A. To allow for out-of-order packets that could arrive after the FIN/ACK packets
- B. To finish any inspection operations
- C. To remove the NAT operation
- D. To generate logs
Answer:
A
Explanation:
TCP provides the ability for one end of a connection to terminate its output while still receiving data
from the other end. This is called a half-close. FortiGate unit implements a specific timer before
removing an entry in the firewall session table.
Question 8
Which two protocols are used to enable administrator access of a FortiGate device? (Choose two.)
- A. SSH
- B. HTTPS
- C. FTM
- D. FortiTelemetry
Answer:
AB
Explanation:
Reference:
https://docs.fortinet.com/document/fortigate/6.4.0/hardening-your-
fortigate/995103/buildingsecurity-into-fortios
Question 9
Refer to the exhibit.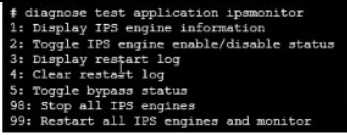
Examine the intrusion prevention system (IPS) diagnostic command.
Which statement is correct If option 5 was used with the IPS diagnostic command and the outcome
was a decrease in the CPU usage?
- A. The IPS engine was inspecting high volume of traffic.
- B. The IPS engine was unable to prevent an intrusion attack .
- C. The IPS engine was blocking all traffic.
- D. The IPS engine will continue to run in a normal state.
Answer:
A
Explanation:
fortinet-fortigate-security-study-guide-for-fortios-72 page 417 If there are high-CPU use problems
caused by the IPS, you can use the diagnose test application ipsmonitor command with option 5 to
isolate where the problem might be. Option 5 enables IPS bypass mode. In this mode, the IPS engine
is still running, but it is not inspecting traffic. If the CPU use decreases after that, it usually indicates
that the volume of traffic being inspected is too high for that FortiGate model.
Reference:
https://docs.fortinet.com/document/fortigate/6.2.3/cookbook/232929/troubleshooting-high-cpu-
usage
Question 10
By default, FortiGate is configured to use HTTPS when performing live web filtering with FortiGuard
servers.
Which CLI command will cause FortiGate to use an unreliable protocol to communicate with
FortiGuard servers for live web filtering?
- A. set fortiguard-anycast disable
- B. set webfilter-force-off disable
- C. set webfilter-cache disable
- D. set protocol tcp
Answer:
A
Explanation:
y default, "fortiguard-anycast" is enabled, and this setting only works with "set protocol https". To
use udp (ie. "set protocol udp"), "fortiguard-anycast" must be disabled.
Reference: https://kb.fortinet.com/kb/documentLink .do?externalID=FD48294
"By default, FortiGate is configured to enforce the use of HTTPS port 443 to perform live filtering with
FortiGuard or FortiManager. Other ports and protocols are available by disabling the FortiGuard
anycast setting on the CLI."
Question 11
How does FortiGate act when using SSL VPN in web mode?
- A. FortiGate acts as an FDS server.
- B. FortiGate acts as an HTTP reverse proxy.
- C. FortiGate acts as DNS server.
- D. FortiGate acts as router.
Answer:
B
Explanation:
Reference:
https://pub.kb.fortinet.com/ksmcontent/Fortinet-Public/current/Fortigate_v4.0MR3/fortigate-
sslvpn-40-mr3.pdf
Question 12
Which three statements explain a flow-based antivirus profile? (Choose three.)
- A. Flow-based inspection uses a hybrid of the scanning modes available in proxy-based inspection.
- B. If a virus is detected, the last packet is delivered to the client.
- C. The IPS engine handles the process as a standalone.
- D. FortiGate buffers the whole file but transmits to the client at the same time.
- E. Flow-based inspection optimizes performance compared to proxy-based inspection.
Answer:
ADE
Explanation:
Reference: https://forum .fortinet.com/tm .aspx?m=192309
Question 13
Refer to the exhibits to view the firewall policy (Exhibit A) and the antivirus profile (Exhibit B).
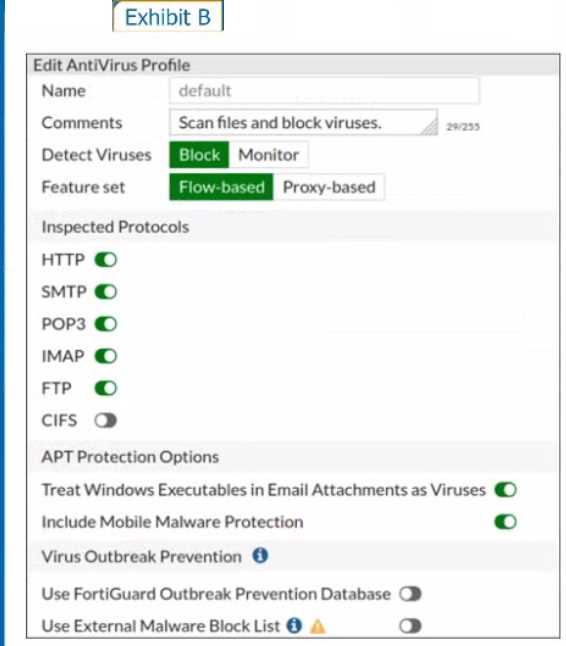
Which statement is correct if a user is unable to receive a block replacement message when
downloading an infected file for the first time?
- A. The firewall policy performs the full content inspection on the file.
- B. The flow-based inspection is used, which resets the last packet to the user.
- C. The volume of traffic being inspected is too high for this model of FortiGate.
- D. The intrusion prevention security profile needs to be enabled when using flow-based inspection mode.
Answer:
B
Explanation:
· "ONLY" If the virus is detected at the "START" of the connection, the IPS engine sends the block
replacement message immediately
· When a virus is detected on a TCP session (FIRST TIME), but where "SOME PACKETS" have been
already forwarded to the receiver, FortiGate "resets the connection" and does not send the last
piece of the file. Although the receiver got most of the file content, the file has been truncated and
therefore, can't be opened. The IPS engine also caches the URL of the infected file, so that if a
"SECOND ATTEMPT" to transmit the file is made, the IPS engine will then send a block replacement
message to the client instead of scanning the file again.
In flow mode, the FortiGate drops the last packet killing the file. But because of that the block
replacement message cannot be displayed. If the file is attempted to download again the block
message will be shown.
Question 14
A network administrator wants to set up redundant IPsec VPN tunnels on FortiGate by using two
IPsec VPN tunnels and static routes.
* All traffic must be routed through the primary tunnel when both tunnels are up
* The secondary tunnel must be used only if the primary tunnel goes down
* In addition, FortiGate should be able to detect a dead tunnel to speed up tunnel failover
Which two key configuration changes are needed on FortiGate to meet the design requirements?
(Choose two,)
- A. Configure a high distance on the static route for the primary tunnel, and a lower distance on the static route for the secondary tunnel.
- B. Enable Dead Peer Detection.
- C. Configure a lower distance on the static route for the primary tunnel, and a higher distance on the static route for the secondary tunnel.
- D. Enable Auto-negotiate and Autokey Keep Alive on the phase 2 configuration of both tunnels.
Answer:
BC
Explanation:
Study Guide – IPsec VPN – IPsec configuration – Phase 1 Network.
When Dead Peer Detection (DPD) is enabled, DPD probes are sent to detect a failed tunnel and bring
it down before its IPsec SAs expire. This failure detection mechanism is very useful when you have
redundant paths to the same destination, and you want to failover to a backup connection when the
primary connection fails to keep the connectivity between the sites up.
There are three DPD modes. On demand is the default mode.
Study Guide – IPsec VPN – Redundant VPNs.
Add one phase 1 configuration for each tunnel. DPD should be enabled on both ends.
Add at least one phase 2 definition for each phase 1.
Add one static route for each path. Use distance or priority to select primary routes over backup
routes (routes for the primary VPN must have a lower distance or lower priority than the backup).
Alternatively, use dynamic routing.
Configure FW policies for each IPsec interface.
Question 15
Which engine handles application control traffic on the next-generation firewall (NGFW) FortiGate?
- A. Antivirus engine
- B. Intrusion prevention system engine
- C. Flow engine
- D. Detection engine
Answer:
B
Explanation:
http://docs.fortinet.com/document/fortigate/6.0.0/handbook/240599/application-control
Reference: http://docs.fortinet.com/document/fortigate/6.0.0/handbook/240599/application-
control