cisco 400-251 practice test
CCIE Security Written Exam
Question 1
A server with IP address 209.165.202.150 is protected behind the inside interface of a Cisco ASA and
the Internet on the outside interface. User on the Internet need to access the server ay any time, but
the firewall administrator does not want to apply NAT to the address of the server because it is
currently a public address. Which three of the following commands can be used to accomplish this?
(Choose three.)
- A. static (outside, inside) 209.165.202.150.209.165.202.150 netmask 255.255.255.255
- B. nat (inside) 1 209.165.202.150 255.255.255.255
- C. static (inside, outside) 209.165.202.150.209.165.202.150 netmask 255.255.255.255
- D. no nat-control
- E. access-list no-nat permit ip host 209.165.202.150 any nat (inside) 0 access-list no-nat
- F. nat (inside) 0 209.165.202.150 255.255.255.255
Answer:
CEF
Question 2
Which statement about the Cisco AMP Virtual Private Cloud Appliance is true for deployments in air-
gapmode?
- A. The amp-sync tool syncs the threat-intelligence repository on the appliance directly with the AMP public cloud.
- B. The appliance can perform disposition lookup against either the Protect DB or the AMP public cloud.
- C. The appliance can perform disposition lookups against the Protect DB without an Internet connection.
- D. The appliance evaluates files against the threat intelligence and disposition information residing on the Update Host.
- E. The Update Host automatically downloads updates and deploys them to the Protect DB on a daily basis.
Answer:
C
Question 3
What are the most common methods that security auditors use to access an organization’s security
processes? (Choose two.)
- A. physical observation
- B. social engineering attempts
- C. penetration testing
- D. policy assessment
- E. document review
- F. interviews
Answer:
AF
Question 4
Which two statements about Cisco AMP for Web Security are true? (Choose two.)
- A. It can prevent malicious data exfiltration by blocking critical files from exiting through the Web gateway.
- B. It can perform reputation-based evaluation and blocking by uploading the fingerprint of incoming files to a cloud-based threat intelligence network.
- C. It can detect and block malware and other anomalous traffic before it passes through the Web gateway.
- D. It can perform file analysis by sandboxing known malware and comparing unknown files to a local repository of the threats.
- E. It can identify anomalous traffic passing through the Web gateway by comparing it to an established of expected activity.
- F. It continues monitoring files after they pass the Web gateway.
Answer:
BF
Question 5
Which three statements about WCCP are true? (Choose three.)
- A. The minimum WCCP-Fast Timers messages interval is 500 ms
- B. Is a specific capability is missing from the Capabilities Info component, the router is assumed to support the default capability
- C. If the packet return method is missing from a packet return method advertisement, the web cache uses the Layer 2 rewrite method
- D. The router must receive a valid receive ID before it negotiates capabilities
- E. The assignment method supports GRE encapsulation for sending traffic
- F. The web cache transmits its capabilities as soon as it receives a receive ID from router
Answer:
ACE
Explanation:
Web Cache Communication Protocol (WCCP)
http://www.cisco.com/c/en/us/td/docs/security/asa/special/wccp/guide/asa-wccp.html
Question 6
What are two features that helps to mitigate man-in-the-middle attacks? (Choose two.)
- A. DHCP snooping
- B. ARP spoofing
- C. destination MAC ACLs
- D. dynamic ARP inspection
- E. ARP sniffing on specific ports
Answer:
AD
Question 7
Refer to the exhibit.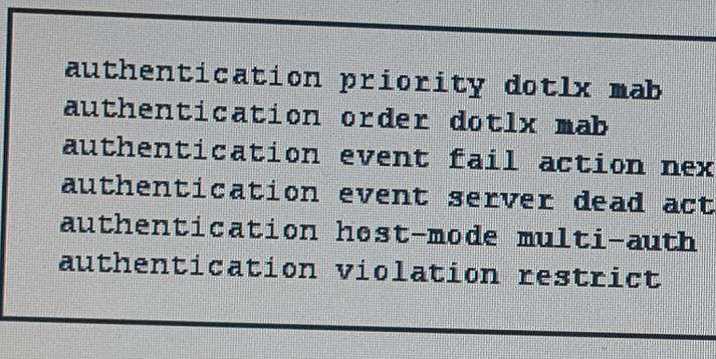
Which two effects of this configuration are true? (Choose two.)
- A. The switch periodically sends an EAP-Identity-Request to the endpoint supplicant.
- B. The device allows multiple authenticated sessions for a single MAC address in the voice domain.
- C. If the TACACS+ server is unreachable, the switch places hosts on critical ports in VLAN 50.
- D. If the authentication priority is changed, the order in which authentication is performed also changes.
- E. If multiple hosts have authenticated to the same port, each can be in their own assigned VLAN.
- F. The port attempts 802.1x authentication first, and then falls back to MAC authentication bypass.
Answer:
CF
Question 8
Which two statements about 6to4 tunneling are true? (Choose two.)
- A. It provides a /128 address block.
- B. It supports static and BGPV4 routing.
- C. It provides a /48 address block.
- D. It supports managed NAT along the path of the tunnel.
- E. The prefix address of the tunnel is determined by the IPv6 configuration of the interface.
- F. It supports multihoming.
Answer:
BC
Question 9
Which three statements about RLDP are true? (Choose three.)
- A. It detects rogue access points that are connected to the wired network.
- B. It can detect rogue APs that use WPA encryption.
- C. It can detect rogue APs operating only on 5 GHz.
- D. It can detect rogue APs that use WEP encryption.
- E. The AP is unable to serve clients while the RLDP process is active.
- F. Active Rogue Containment can be initiated manually against rogue devices detected on the wired network.
Answer:
AEF
Explanation:
Rogue Location Discovery Protocol (RLDP)
http://www.cisco.com/c/en/us/support/docs/wireless-mobility/wireless-lan-wlan/70987-rogue-detect.html
Question 10
What are three features that are enabled by generating Change of Authorization (CoA) requests in a
push model? (Choose three.)
- A. session reauthentication
- B. session identification
- C. host reauthentication
- D. MAC identification
- E. session termination
- F. host termination
Answer:
BCE
Question 11
Refer to the exhibit.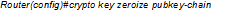
Which effect of this command is true?
- A. The route immediately deletes its current public key from the cache and generates a new one.
- B. The public key of the remote peer is deleted from the router cache.
- C. The CA revokes the public key certificate of the router.
- D. The current public key of the router is deleted from the cache when the router reboots, and the router generates a new one.
- E. The router sends a request to the CA to delete the router certificate from its configuration.
Answer:
B
Question 12
Which two statements about a wireless access point configured with the guest-mode command are
true?
(Choose two.)
- A. It can support more than one guest-mode SSID.
- B. It supports associations by clients that perform passive scans.
- C. It allows clients configured without SSIDs to associate.
- D. It allows associated clients to transmit packets using its SSID.
- E. If one device on a network is configure in guest-mode, clients can use the guest-mode SSID to connect to any device in the same network.
Answer:
BC
Question 13
Refer to the exhibit.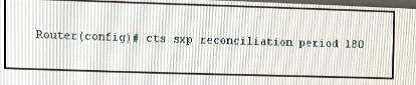
Which two statements about a device with this configuration are true? (Choose two.)
- A. When a peer establishes a new connection to the device, CTS retains all existing SGT mapping entries for 3 minutes.
- B. If a peer reconnects to device within 120 seconds of terminating a CTS-SXP connection, the reconciliation timer stats.
- C. When a peer re-establishes a previous connection to the device, CTS retains all existing SGT mapping entries for 3 minutes.
- D. If a peer reconnects to device within 180 seconds of terminating a CTS-SXP connection, the reconciliation timer stats.
- E. If a peer re-establishes a connection to the device before the hold-down timer expires, the device retains the SGT mapping entries it learned during the previous connection for an additional 3 minutes.
- F. It sets the internal hold-down timer of the device to 3 minutes.
Answer:
BE
Question 14
Which option is a data modeling language used to model configuration and state data of network
elements?
- A. RESTCONF
- B. SNMPv4
- C. NETCONF
- D. YANG
Answer:
D
Question 15
Which statement about MDM with the Cisco ISE is true?
- A. The MDM’s server certificate must be imported into the Cisco ISE Certificate Store before the MDM and ISE can establish a connection.
- B. MDM servers can generate custom ACLs for the Cisco ISE to apply to network devices.
- C. The Cisco ISE supports a built-in list of MDM dictionary attributes it can use in authorization policies.
- D. The Cisco ISE supports limited built-in MDM functionality.
- E. If a mobile endpoint fails posture compliance, both the user and the administrator are notified immediately.
- F. When a mobile endpoint becomes compliant the Cisco ISE records the updated device status in its internal database.
Answer:
A
Explanation:
Mobile Device Management
https://meraki.cisco.com/blog/tag/mobile-device-management/