arcitura education s90-08b practice test
SOA Design & Architecture Lab with Services & Microservices
Question 1
Refer to Exhibit.
Service A is a task service that sends Service B a message (2) requesting that Service B return data
back to Service A in a response message (3). Depending on the response received, Service A may be
required to send a message to Service C (4) for which it requires no response.
Before it contacts Service B, Service A must first retrieve a list of code values from its own database
(1) and then place this data into its own memory. If it turns out that it must send a message to
Service C, then Service A must combine the data it receives from Service B with the data from the
code value list in order to create the message it sends to Service C. If Service A is not required to
invoke Service C, it can complete its task by discarding the code values.
Service A and Service C reside in Service Inventory
- A. The Data Model Transformation pattern can be applied by establishing an intermediate processing layer between Service A and Service B that can transform a message from one data model to another at runtime. The Intermediate Routing and Service Agent patterns can be applied so that when Service B sends a response message, a service agent can intercept the message and, based on its contents, either forward the message to Service A or route the message to Service C. The Service Autonomy principle can be further applied to Service C together with the Redundant Implementation pattern to help establish a more reliable and scalable service architecture.
- B. The Data Format Transformation pattern can be applied by establishing an intermediate processing layer between Service A and Service B that can transform a message from one data format to another at runtime. The Asynchronous Queuing pattern can be applied to establish an intermediate queue between Service A and Service C so that when Service A needs to send a message to Service C, the queue will store the message and retransmit it to Service C until it is successfully delivered. The Service Autonomy principle can be further applied to Service C together with the Redundant Implementation pattern to help establish a more reliable and scalable service architecture.
- C. The Data Model Transformation pattern can be applied by establishing an intermediate processing layer between Service A and Service B that can transform a message from one data model to another at runtime. The Intermediate Routing and Service Agent patterns can be applied so that when Service B sends a response message, a service agent can intercept the message and, based on its contents, either forward the message to Service A or route the message to Service C. The Service Statelessness principle can be applied with the help of the State Repository pattern so that Service A can write the code value data to a state database while it is waiting for Service B to respond.
- D. The Data Format Transformation pattern can be applied by establishing an intermediate processing layer between Service A and Service B that can transform a message from one data format to another at runtime. The Asynchronous Queuing pattern can be applied to establish an intermediate queue between Service A and Service B so that when Service A needs to send a message to Service B, the queue will store the message and retransmit it to Service B until it is successfully delivered. The Service Reusability principle can be further applied to Service C together with the Redundant Implementation pattern to help establish a more reusable and scalable service architecture.
Answer:
B
Explanation:
The problem is that Service A and Service B are using different technologies and cannot
communicate. Therefore, an intermediate processing layer can be established that can transform
messages from one data format to another at runtime. This can be achieved using the Data Format
Transformation pattern.
Additionally, Service C frequently reaches its usage thresholds and is not always available, so an
Asynchronous Queuing pattern can be applied to establish an intermediate queue between Service A
and Service C. This queue will store the messages sent by Service A to Service C and retransmit them
until they are successfully delivered. This approach improves the reliability of the system.
Moreover, the Redundant Implementation pattern can be applied to Service C to ensure its
availability and scalability, and the Service Autonomy principle can be applied to make Service C
independent of other services.
Question 2
Refer to Exhibit.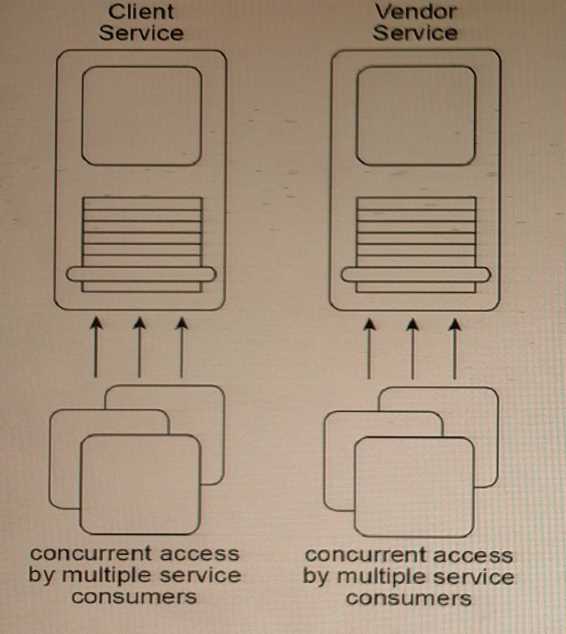
The Client and Vendor services are agnostic services that are both currently part of multiple service
compositions. As a result, these services are sometimes subjected to concurrent access by multiple
service consumers.
The Client service primarily provides data access logic to a client database but also coordinates with
other services to determine a clients credit rating. The Vendor service provides some data access
logic but can also generate various dynamic reports based on specialized business requirements.
After reviewing historical statistics about the runtime activity of the two services, it is discovered that
the Client service is serving an ever-increasing number of service consumers. It is regularly timing
out, which in turn increases its call rate as service consumers retry their requests. The Vendor service
occasionally has difficulty meeting its service-level agreement (SLA) and when this occurs, penalties
are assessed.
Recently, the custodian of the Client service was notified that the Client service will be made
available to new service consumers external to its service inventory. The Client service will be
providing free credit rating scores to any service consumer that connects to the service via the
Internet. The Vendor service will remain internal to the service inventory and will not be exposed to
external access.
Which of the following statements describes a solution that addresses these issues and
requirements?
- A. The API Gateway pattern, together with the Inventory Endpoint pattern, can be applied to the service inventory to establish an inventory endpoint service and an intermediary layer of processing that will be accessed by external service consumers and that will interact with the Client service to process external service consumer requests. The Redundant Implementation pattern can be applied to both the Client and Vendor services to increase their availability and scalability.
- B. The Official Endpoint pattern can be applied to the Client service to establish a managed endpoint for consumption by service consumers external to the service inventory. The Concurrent Contracts pattern can be applied to the Vendor service, enabling it to connect with alternative Client service implementation, should the first attempt to connect fail.
- C. The State Repository pattern can be applied to the Client and Vendor services to establish a central statement management database that can be used to overcome runtime performance problems. The Official Endpoint pattern can be further applied to increase the availability and scalability of the Client service for service consumers external to the service inventory.
- D. The Microservice Deployment pattern is applied to the Client service to improve its autonomy and responsiveness to a greater range of service consumers. The Containerization pattern is applied to the Vendor service to establish a managed environment with a high degree of isolation for its report- related processing. The Endpoint Redirection pattern is further applied to ensure that request messages from service consumers outside of the service inventory are redirected away from the Client service.
Answer:
A
Explanation:
This solution addresses the specific requirements and issues identified in the scenario. The Official
Endpoint pattern can be applied to the Client service to establish a managed endpoint for
consumption by service consumers external to the service inventory, which will allow for controlled
and managed access to the service. The Concurrent Contracts pattern can be applied to the Vendor
service, which will enable it to connect with alternative Client service implementation if the first
attempt to connect fails, thereby increasing its availability and reducing the possibility of penalties
being assessed due to not meeting its SLA.
Question 3
Refer to Exhibit.
Service A is an entity service that provides a set of generic and reusable service capabilities. In order
to carry out the functionality of any one of its service capabilities, Service A is required to compose
Service B (1) and Service C (2), and Service A is required to access Database A (3), Database B (4), and
Database C (5). These three databases are shared by other applications within the IT enterprise.
All of service capabilities provided by Service A are synchronous, which means that for each request
a service consumer makes, Service A is required to issue a response message after all of the
processing has completed.
Service A is one of many entity services that reside In a highly normalized service Inventory. Because
Service A provides agnostic logic, it is heavily reused and is currently part of many service
compositions.
You are told that Service A has recently become unstable and unreliable. The problem has been
traced to two issues with the current service architecture. First, Service B, which Is also an entity
service, is being increasingly reused and has itself become unstable and unreliable. When Service B
fails, the failure is carried over to Service
- A. The Redundant Implementation pattern can be applied to Service A, thereby making duplicate deployments of the service available. This way, when one implementation of Service A is too busy, another implementation can be accessed by service consumers instead. The Service Data Replication pattern can be applied to establish a dedicated database that contains an exact copy of the data from shared Database B that is required by Service A.
- B. The Redundant Implementation pattern can be applied to Service B, thereby making duplicate deployments of the service available. This way, when one implementation of Service B is too busy, another implementation can be accessed by Service A instead. The Data Model Transformation pattern can be applied to establish a dedicated database that contains an exact copy of the data from shared Database B that is required by Service A.
- C. The Redundant Implementation pattern can be applied to Service B, thereby making duplicate deployments of the service available. This way, when one implementation of Service B is too busy, another implementation can be accessed by Service A instead. The Service Data Replication pattern can be applied to establish a dedicated database that contains a copy of the data from shared Database B that is required by Service A. The replicated database is designed with an optimized data model to improve query execution performance.
- D. The Redundant Implementation pattern can be applied to Service A, thereby making duplicate deployments of the service available. This way, when one implementation of Service A is too busy, another implementation can be accessed by service consumers instead. The Service Statelessness principle can be applied with the help of the State Repository pattern In order to establish a state database that Service A can use to defer state data it may be required to hold for extended periods, thereby improving its availability and scalability.
Answer:
C
Explanation:
This solution addresses both issues with the current service architecture. By applying the Redundant
Implementation pattern to Service B, duplicate deployments of the service are made available,
ensuring that when one implementation fails, another can be accessed by Service A. Additionally, the
Service Data Replication pattern can be applied to establish a dedicated database that contains a
copy of the data from shared Database B that is required by Service A. This replicated database is
designed with an optimized data model to improve query execution performance, ensuring that
queries issued by Service A to the database can complete more quickly, improving the overall
stability and reliability of Service A. By applying these patterns, the problems with Service A can be
solved without compromising the normalization of the service inventory.
Question 4
Refer to Exhibit.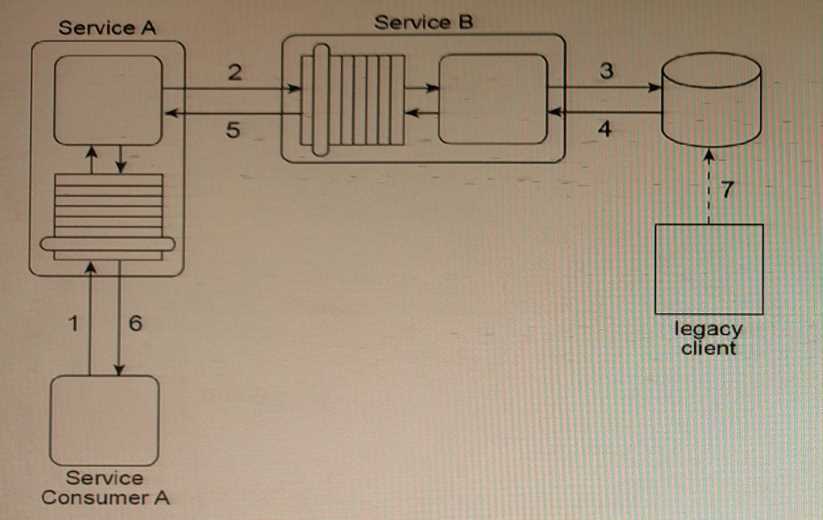
Service A is an entity service that provides a Get capability which returns a data value that is
frequently changed.
Service Consumer A invokes Service A in order to request this data value (1). For Service A to carry
out this request, it must invoke Service B (2), a utility service that interacts (3, 4) with the database in
which the data value is stored. Regardless of whether the data value changed, Service B returns the
latest value to Service A (5), and Service A returns the latest value to Service Consumer A (6).
The data value is changed when the legacy client program updates the database (7). When this
change will occur is not predictable. Note also that Service A and Service B are not always available at
the same time.
Any time the data value changes, Service Consumer A needs to receive It as soon as possible.
Therefore, Service Consumer A initiates the message exchange shown In the figure several times a
day. When it receives the same data value as before, the response from Service A Is ignored. When
Service A provides an updated data value, Service Consumer A can process it to carry out its task.
The current service composition architecture is using up too many resources due to the repeated
invocation of Service A by Service Consumer A and the resulting message exchanges that occur with
each invocation.
What steps can be taken to solve this problem?
- A. The Event-Driven Messaging pattern can be applied by establishing a subscriber-publisher relationship between Service A and Service B. This way, every time the data value is updated, an event is triggered and Service B, acting as the publisher, can notify Service A, which acts as the subscriber. The Asynchronous Queuing pattern can be applied between Service A and Service B so that the event notification message sent out by Service B will be received by Service A, even when Service A is unavailable.
- B. The Event-Driven Messaging pattern can be applied by establishing a subscriber-publisher relationship between Service Consumer A and Service A. This way, every time the data value is updated, an event is triggered and Service A, acting as the publisher, can notify Service Consumer A, which acts as the subscriber. The Asynchronous Queuing pattern can be applied between Service Consumer A and Service A so that the event notification message sent out by Service A will be received by Service Consumer A, even when Service Consumer A is unavailable.
- C. The Asynchronous Queuing pattern can be applied so that messaging queues are established between Service A and Service B and between Service Consumer A and Service A. This way, messages are never lost due to the unavailability of Service A or Service B.
- D. The Event-Driven Messaging pattern can be applied by establishing a subscriber -publisher relationship between Service Consumer A and a database monitoring agent introduced through the application of the Service Agent pattern. The database monitoring agent monitors updates made by the legacy client to the database. This way, every time the data value is updated, an event is triggered and the database monitoring agent, acting as the publisher, can notify Service Consumer A, which acts as the subscriber. The Asynchronous Queuing pattern can be applied between Service Consumer A and the database monitoring agent so that the event notification message sent out by the database monitoring agent will be received by Service Consumer A, even when Service Consumer A is unavailable.
Answer:
A
Explanation:
This solution is the most appropriate one among the options presented. By using the Event-Driven
Messaging pattern, Service A can be notified of changes to the data value without having to be
invoked repeatedly by Service Consumer A, which reduces the resources required for message
exchange. Asynchronous Queuing ensures that the event notification message is not lost due to the
unavailability of Service A or Service B. This approach improves the efficiency of the service
composition architecture.
Question 5
Refer to Exhibit.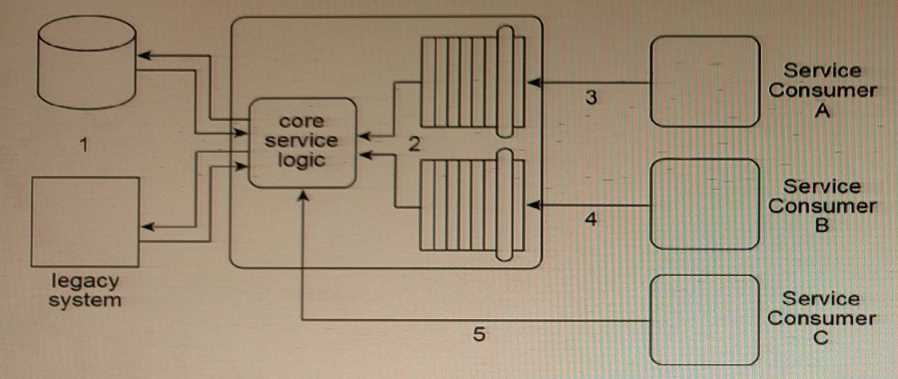
The architecture for Service A displayed in the figure shows how the core logic of Service A has
expanded over time to connect to a database and a proprietary legacy system (1), and to support two
separate service contracts (2) that are accessed by different service consumers.
The service contracts are fully decoupled from the service logic. The service logic is therefore coupled
to the service contracts and to the underlying implementation resources (the database and the
legacy system).
Service A currently has three service consumers. Service Consumer A and Service Consumer B access
Service A's two service contracts (3, 4). Service Consumer C bypasses the service contracts and
accesses the service logic directly (5).
You are told that the database and legacy system that are currently being used by Service A are being
replaced with different products. The two service contracts are completely decoupled from the core
service logic, but there is still a concern that the introduction of the new products will cause the core
service logic to behave differently than before.
What steps can be taken to change the Service A architecture in preparation for the introduction of
the new products so that the impact on Service Consumers A and B is minimized? What further step
can be taken to avoid consumer-to-implementation coupling with Service Consumer C?
- A. The Service Fagade pattern can be applied to position fagade components between the core service logic and Service Consumers A and B. These fagade components will be designed to regulate the behavior of Service A. The Service Abstraction principle can be applied to hide the implementation details of the core service logic of Service A, thereby shielding this logic from changes to the implementation. The Schema Centralization pattern can be applied to force Service Consumer C to access Service A via one of its existing service contracts.
- B. A third service contract can be added together with the application of the Contract Centralization pattern. This will force Service Consumer C to access Service A via the new service contract. The Service Fagade pattern can be applied to position a fagade component between the new service contract and Service Consumer C in order to regulate the behavior of Service A. The Service Abstraction principle can be applied to hide the implementation details of Service A so that no future service consumers are designed to access any of Service A's underlying resources directly.
- C. The Service Fagade pattern can be applied to position fagade components between the core service logic and the two service contracts. These fagade components will be designed to regulate the behavior of Service A. The Service Loose Coupling principle can be applied to avoid negative forms of coupling.
- D. The Service Fagade pattern can be applied to position fagade components between the core service logic and the implementation resources (the database and the legacy system). These fagade components will be designed to insulate the core service logic of Service A from the changes in the underlying implementation resources. The Schema Centralization and Endpoint Redirection patterns can also be applied to force Service Consumer C to access Service A via one of its existing service contracts.
Answer:
D
Explanation:
The Service Fagade pattern can be applied to position fagade components between the core service
logic and the implementation resources (the database and the legacy system). These fagade
components will be designed to insulate the core service logic of Service A from the changes in the
underlying implementation resources. This will minimize the impact of the introduction of the new
products on Service Consumers A and B since the service contracts are fully decoupled from the core
service logic. The Schema Centralization and Endpoint Redirection patterns can also be applied to
force Service Consumer C to access Service A via one of its existing service contracts, avoiding direct
access to the core service logic and the underlying implementation resources.
Question 6
Refer to Exhibit.
When Service A receives a message from Service Consumer A (1), the message is processed by
Component
- A. The Legacy Wrapper pattern can be applied so that Component B is separated into a separate wrapper utility service that wraps the shared database. The Asynchronous Queuing pattern can be applied so that a messaging queue is positioned between Component A and Component C, thereby enabling communication during the times when the legacy system may be unavailable or heavily accessed by other parts of the IT enterprise. The Service Fagade pattern can be applied so that a fagade component is added between Component A and Component D so that any change In behavior can be compensated. The Service Autonomy principle can be further applied to Service A to help make up for any performance loss that may result from splitting the component into a separate wrapper utility service.
- B. The Legacy Wrapper pattern can be applied so that Component B Is separated into a separate utility service that wraps the shared database. The Legacy Wrapper pattern can be applied again so that Component C is separated into a separate utility service that acts as a wrapper for the legacy system API. The Legacy Wrapper pattern can be applied once more to Component D so that it is separated into another utility service that provides standardized access to the file folder. The Service Fagade pattern can be applied so that three fagade components are added: one between Component A and each of the new wrapper utility services. This way, the fagade components can compensate for any change in behavior that may occur as a result of the separation. The Service Composability principle can be further applied to Service A and the three new wrapper utility services so that all four services are optimized for participation in the new service composition. This will help make up for any performance loss that may result from splitting the three components into separate services.
- C. The Legacy Wrapper pattern can be applied so that Component B is separated into a separate utility service that wraps the shared database. The Legacy Wrapper pattern can be applied again so that Component C is separated into a separate utility service that acts as a wrapper for the legacy system API. Component D can also be separated into a separate service and the Event-Driven Messaging pattern can be applied to establish a publisher-subscriber relationship between this new service and Component A. The interaction between Service Consumer A and Component A can then be redesigned so that Component A first interacts with Component B and the new wrapper service. Service A then issues a final message back to Service Consumer A. The Service Composability principle can be further applied to Service A and the three new wrapper utility services so that all four services are optimized for participation in the new service composition. This will help make up for any performance loss that may result from splitting the three components into separate services.
- D. The Legacy Wrapper pattern can be applied so that Component B is separated into a separate wrapper utility service that wraps the shared database. The State Repository and State Messaging patterns can be applied so that a messaging repository is positioned between Component A and Component C, thereby enabling meta data-driven communication during the times when the legacy system may be unavailable or heavily accessed by other parts of the IT enterprise. The Service Fagade pattern can be applied so that a fagade component is added between Component A and Component D so that any change in behavior can be compensated. The Service Statelessness principle can be further applied to Service A to help make up for any performance loss that may result from splitting the component into a separate wrapper utility service.
Answer:
B
Question 7
Refer to Exhibit.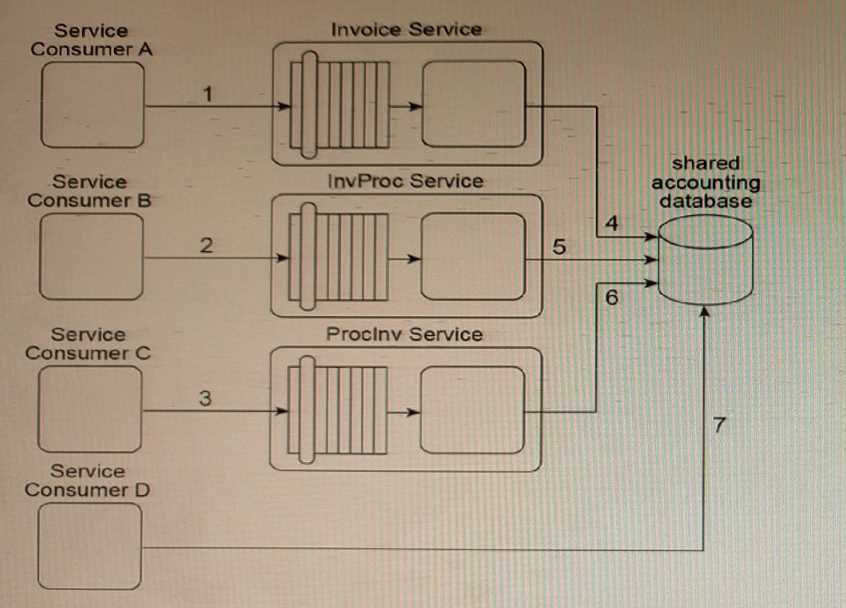
Our service inventory contains the following three services that provide Invoice-related data access
capabilities: Invoice, InvProc and Proclnv. These services were created at different times by different
project teams and were not required to comply with any design standards. Therefore, each of these
services has a different data model for representing invoice data.
Currently, each of these three services has a different service consumer: Service Consumer A
accesses the Invoice service (1), Service Consumer B (2) accesses the InvProc service, and Service
Consumer C (3) accesses the Proclnv service. Each service consumer invokes a data access capability
of an invoice-related service, requiring that service to interact with the shared accounting database
that is used by all invoice-related services (4, 5, 6).
Additionally, Service Consumer D was designed to access invoice data from the shared accounting
database directly (7). (Within the context of this architecture, Service Consumer D is labeled as a
service consumer because it is accessing a resource that is related to the illustrated service
architectures.)
Assuming that the Invoice service, InvProc service and Proclnv service are part of the same service
inventory, what steps would be required to fully apply the Official Endpoint pattern?
- A. One of the invoice-related services needs to be chosen as the official service providing invoice data access capabilities. Service Consumers A, B, and C then need to be redesigned to only access the chosen invoice-related service. Because Service Consumer D does not rely on an invoice-related service, it is not affected by the Official Endpoint pattern and can continue to access the accounting database directly. The Service Abstraction principle can be further applied to hide the existence of the shared accounting database and other implementation details from current and future service consumers.
- B. One of the invoice-related services needs to be chosen as the official service providing invoice data access capabilities and logic from the other two services needs to be moved to execute within the context of the official Invoice service. Service Consumers A, B, and C then need to be redesigned to only access the chosen invoice-related service. Service Consumer D also needs to be redesigned to not access the shared accounting database directly, but to also perform its data access by interacting with the official invoice-related service. The Service Abstraction principle can be further applied to hide the existence of the shared accounting database and other implementation details from current and future service consumers.
- C. Because Service Consumers A, B, and C are already carrying out their data access via published contracts, they are not affected by the Official Endpoint pattern. Service Consumer D needs to be redesigned so that it does not access the shared accounting database directly, but instead performs its data access by interacting with the official invoice-related service. The Service Abstraction principle can be further applied to hide the existence of the shared accounting database and other implementation details from current and future service consumers.
- D. One of the invoice-related services needs to be chosen as the official service providing invoice data access capabilities. Because Service Consumer D does not rely on an invoice-related service, it is not affected by the Official Endpoint pattern and can continue to access the accounting database directly. The Service Loose Coupling principle can be further applied to decouple Service Consumers A, B, and C from the shared accounting database and other implementation details.
Answer:
B
Explanation:
he Legacy Wrapper pattern can be applied so that Component B is separated into a separate utility
service that wraps the shared database. The Legacy Wrapper pattern can be applied again so that
Component C is separated into a separate utility service that acts as a wrapper for the legacy system
API. The Legacy Wrapper pattern can be applied once more to Component D so that it is separated
into another utility service that provides standardized access to the file folder. The Service Facade
pattern can be applied so that three facade components are added: one between Component A and
each of the new wrapper utility services. This way, the facade components can compensate for any
change in behavior that may occur as a result of the separation. The Service Composability principle
can be further applied to Service A and the three new wrapper utility services so that all four services
are optimized for participation in the new service composition. This will help make up for any
performance loss that may result from splitting the three components into separate services.
By applying the Legacy Wrapper pattern to separate Components B, C, and D into three different
utility services, the shared resources within the IT enterprise (Database A, the legacy system, and the
file folders) can be properly encapsulated and managed by dedicated services. The Service Facade
pattern can then be used to create a facade component between Component A and each of the new
wrapper utility services, allowing them to interact seamlessly without affecting Service Consumer A's
behavior.
Finally, the Service Composability principle can be applied to ensure that Service A and the three
new wrapper utility services are optimized for participation in the new service composition. This will
help to mitigate any performance loss that may result from splitting the three components into
separate services.
Question 8
Refer to Exhibit.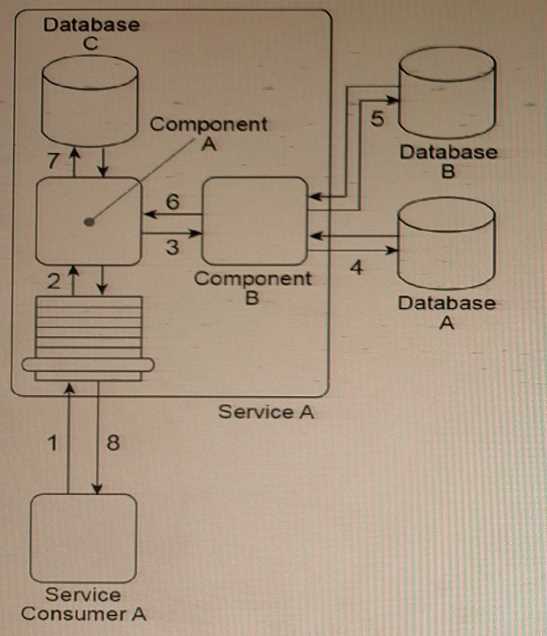
Service Consumer A sends Service A a message containing a business document (1). The business
document is received by Component A, which keeps the business document in memory and forwards
a copy to Component B (3). Component B first writes portions of the business document to Database
A (4). Component B then writes the entire business document to Database B and uses some of the
data values from the business document as query parameters to retrieve new data from Database B
(5).
Next, Component B returns the new date* back to Component A (6), which merges it together with
the original business document it has been keeping in memory and then writes the combined data to
Database C (7). The Service A service capability invoked by Service Consumer A requires a
synchronous request-response data exchange. Therefore, based on the outcome of the last database
update, Service A returns a message with a success or failure code back to Service Consumer A (8).
Databases A and B are shared, and Database C is dedicated to the Service A service architecture.
There are several problems with this architecture. The business document that Component A is
required to keep in memory (while it waits for Component B to complete its processing) can be very
large. The amount of runtime resources Service A uses to keep this data in memory can decrease the
overall performance of all service instances, especially when it is concurrently invoked by multiple
service consumers. Additionally, Service A can take a long time to respond back to Service Consumer
A because Database A is a shared database that sometimes takes a long time to respond to
Component B. Currently, Service Consumer A will wait for up to 30 seconds for a response, after
which it will assume the request to Service A has failed and any subsequent response messages from
Service A will be rejected.
What steps can be taken to solve these problems?
- A. The Service Statelessness principle can be applied together with the State Repository pattern to extend Database C so that it also becomes a state database allowing Component A to temporarily defer the business document data while it waits for a response from Component B. The Service Autonomy principle can be applied together with the Legacy Wrapper pattern to isolate Database A so that it is encapsulated by a separate wrapper utility service. The Compensating Service Transaction pattern can be applied so that whenever Service A's response time exceeds 30 seconds, a notification is sent to a human administrator to raise awareness of the fact that the eventual response of Service A will be rejected by Service Consumer A.
- B. The Service Statelessness principle can be applied together with the State Repository pattern to establish a state database to which Component A can defer the business document data to while it waits for a response from Component B. The Service Autonomy principle can be applied together with the Service Data Replication pattern to establish a dedicated replicated database for Component B to access instead of shared Database A. The Asynchronous Queuing pattern can be applied to establish a message queue between Service Consumer A and Service A so that Service Consumer A does not need to remain stateful while it waits for a response from Service A.
- C. The Service Statelessness principle can be applied together with the State Repository pattern to establish a state database to which Component A can defer the business document data while it waits for a response from Component B. The Service Autonomy principle can be applied together with the Service Abstraction principle, the Legacy Wrapper pattern, and the Service Fagade pattern in order to isolate Database A so that it is encapsulated by a separate wrapper utility service and to hide the Database A implementation from Service A and to position a fagade component between Component B and the new wrapper service. This fagade component will be responsible for compensating the unpredictable behavior of Database A.
- D. None of the above.
Answer:
B
Explanation:
The problems with the current architecture can be addressed by applying the following patterns:
Service Statelessness principle and State Repository pattern - This pattern allows Component A to
defer the business document data to a state database while it waits for a response from Component
B. This helps reduce the amount of runtime resources Service A uses to keep the data in memory and
improves overall performance.
Service Autonomy principle and Service Data Replication pattern - This pattern allows Component B
to access a dedicated replicated database instead of the shared Database A, which can improve
response time.
Asynchronous Queuing pattern - This pattern allows Service A to use a message queue to
communicate with Service Consumer A asynchronously. This means that Service Consumer A does
not need to remain stateful while waiting for a response from Service A, which can improve overall
performance and scalability.
Therefore, option B is the correct answer. Option A is incorrect because it suggests using the
Compensating Service Transaction pattern to raise awareness of the eventual response rejection,
which does not actually solve the problem. Option C is also incorrect because it suggests using
multiple patterns, which may not be necessary and can add unnecessary complexity to the
architecture.
Question 9
Refer to Exhibit.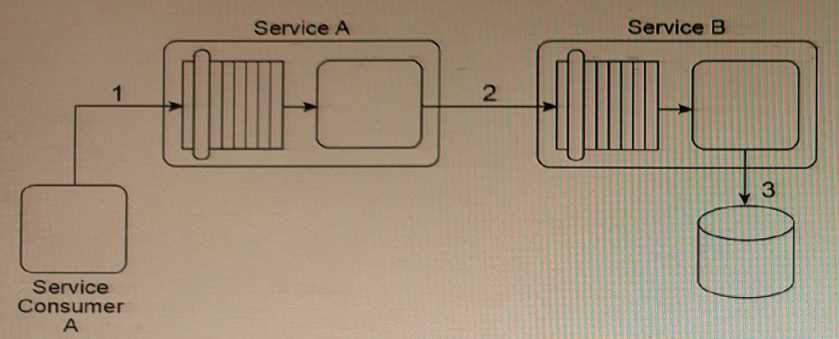
Service A is a SOAP-based Web service with a functional context dedicated to invoice-related
processing. Service B is a REST-based utility service that provides generic data access to a database.
In this service composition architecture, Service Consumer A sends a SOAP message containing an
invoice XML document to Service A (1). Service A then sends the invoice XML document to Service B
(2), which then writes the invoice document to a database (3).
The data model used by Service Consumer A to represent the invoice document is based on XML
Schema
- A. Service Consumer A can be redesigned to use XML Schema B so that the SOAP message it sends is compliant with the service contract of Service A. The Data Model Transformation pattern can then be applied to transform the SOAP message sent by Service A so that it conforms to the XML Schema A used by Service B. The Standardized Service Contract principle must then be applied to Service B and Service Consumer A so that the invoice XML document is optimized to avoid unnecessary validation.
- B. The service composition can be redesigned so that Service Consumer A sends the invoice document directly to Service B after the specialized invoice processing logic from Service A is copied to Service B. Because Service Consumer A and Service B use XML Schema A, the need for transformation logic is avoided. This naturally applies the Service Loose Coupling principle because Service Consumer A is not required to send the invoice document In a format that is compliant with the database used by Service B.
- C. Service Consumer A can be redesigned to write the invoice document directly to the database. This reduces performance requirements by avoiding the involvement of Service A and Service B. It further supports the application of the Service Loose Coupling principle by ensuring that Service Consumer A contains data access logic that couples it directly to the database.
- D. The service composition can be redesigned so that Service Consumer A sends the invoice document directly to Service B. Because Service Consumer A and Service B use XML Schema A, the need for transformation logic is avoided. This naturally applies the Logic Centralization pattern because Service Consumer A is not required to send the invoice document In a format that is compliant with the database used by Service B.
Answer:
A
Explanation:
The recommended solution is to use the Data Model Transformation pattern to transform the invoice
XML document from Schema B to Schema A before passing it to Service B. This solution maintains
the separation of concerns and allows each service to work with its own specific XML schema.
Additionally, the Standardized Service Contract principle should be applied to Service B and Service
Consumer A to ensure that unnecessary validation is avoided, thus optimizing the invoice XML
document. This solution avoids adding logic that will increase the runtime performance
requirements.
Question 10
Refer to Exhibit.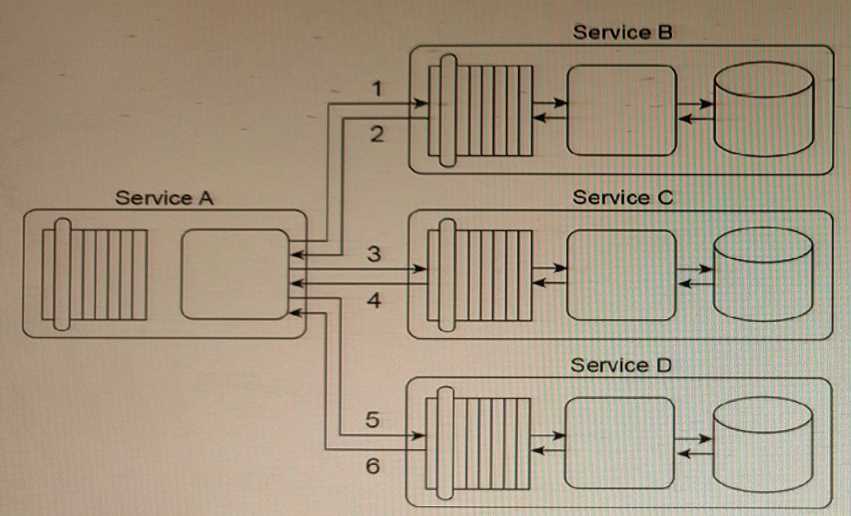
Service A is a task service that is required to carry out a series of updates to a set of databases in
order to complete a task. To perform the database updates. Service A must interact with three other
services that each provides standardized data access capabilities.
Service A sends its first update request message to Service B (1), which then responds with a
message containing either a success or failure code (2). Service A then sends its second update
request message to Service C (3), which also responds with a message containing either a success or
failure code (4). Finally, Service A sends a request message to Service D (5), which responds with its
own message containing either a success or failure code (6).
Services B, C and D are agnostic services that are reused and shared by multiple service consumers.
This has caused unacceptable performance degradation for the service consumers of Service A as it is
taking too long to complete its overall task. You've been asked to enhance the service composition
architecture so that Service A provides consistent and predictable runtime performance. You are
furthermore notified that a new type of data will be introduced to all three databases. It is important
that this data is exchanged in a standardized manner so that the data model used for the data in
inter-service messages is the same.
What steps can be taken to fulfill these requirements?
- A. The Compensating Service Transaction pattern can be applied so that exception logic is executed to notify Service A whenever the data access logic executed by Service B, C, or D takes too long. If the execution time exceeds a predefined limit, then the overall service activity is cancelled and a failure code is returned to Service A. The Schema Centralization pattern is applied to ensure that all services involved in the composition use the same schemas to represented the data consistently.
- B. The Composition Autonomy pattern can be applied to establish an isolated environment in which redundant implementations of Services B, C and D are accessed only by Service A. The Canonical Schema pattern can be applied to ensure that the new type of data is represented by the same data model, regardless of which service sends or receives a message containing the data.
- C. The Redundant Implementation pattern is applied to Service A, along with the Service Instance Routing pattern. This allows for multiple instances of Service A to be created across multiple physical implementations, thereby increasing scalability and availability. The Dual Protocols pattern is applied to all services to support proprietary and standardized data models.
- D. The Service Fagade pattern is applied to all services in order to create an intermediary processing layer within each service architecture. The Content Negotiation pattern is applied so that each service fagade component within each service architecture is equipped with the logic required to defer request messages to other service instances when concurrent usage of the service is high, and to further apply the conversation logic necessary to convert proprietary data from a database into the standardized XML schema format.
Answer:
B
Explanation:
This approach isolates the services used by Service A, allowing it to avoid the performance
degradation caused by multiple service consumers. By creating redundant implementations of
Services B, C, and D that are accessed only by Service A, the Composition Autonomy pattern also
ensures that Service A's runtime performance is consistent and predictable. Applying the Canonical
Schema pattern ensures that the new type of data is exchanged in a standardized manner, ensuring
consistent representation of the data model used for the data in inter-service messages.
Question 11
Refer to Exhibit.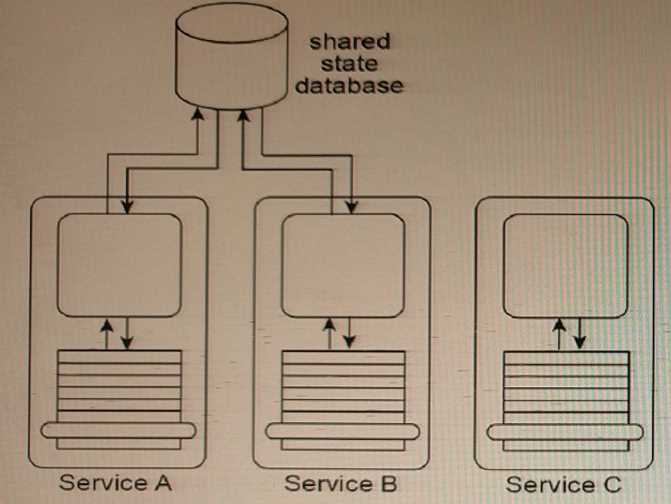
Services A, B, and C are non-agnostic task services. Service A and Service B use the same shared state
database to defer their state data at runtime.
An assessment of the three services reveals that each contains some agnostic logic that cannot be
made available for reuse because it is bundled together with non-agnostic logic.
The assessment also determines that because Service A, Service B and the shared state database are
each located in physically separate environments, the remote communication required for Service A
and Service B to interact with the shared state database is causing an unreasonable decrease in
runtime performance.
How can the application of the Orchestration pattern improve this architecture?
- A. The application of the Orchestration pattern will result in an environment whereby the Official Endpoint, State Repository, and Service Data Replication patterns are automatically applied, allowing the shared state database to be replicated via official service endpoints for Services A and B so that each task service can have its own dedicated state database.
- B. The application of the Orchestration pattern will result in an environment whereby the non- agnostic logic can be cleanly separated from the agnostic logic that exists in Services A, B, and C, resulting in the need to design new agnostic services with reuse potential assured through the application of the Service Reusability principle. The State Repository pattern, which is supported by and local to the orchestration environment, provides a central state database that can be shared by Services A and B. The local state database avoids problems with remote communication.
- C. The application of the Orchestration pattern will result in an environment whereby the Compensating Service Transaction is automatically applied, resulting In the opportunity to create sophisticated exception logic that can be used to compensate for the performance problems caused by Services A and B having to remotely access the state database. The API Gateway and Service Broker patterns are also automatically applied, providing common transformation functions in a centralized processing layer to help overcome any disparity in the service contracts that will need to be created for the new agnostic services.
- D. The Orchestration pattern is not applicable to this architecture because it does not support the hosting of the required state repository.
Answer:
B
Explanation:
The application of the Orchestration pattern can improve this architecture by cleanly separating the
non-agnostic logic from the agnostic logic, allowing the design of new agnostic services with reuse
potential. The State Repository pattern, which is supported by and local to the orchestration
environment, provides a central state database that can be shared by Services A and B. The local
state database avoids problems with remote communication. Additionally, the Orchestration pattern
provides a central controller that can coordinate the interactions between Services A, B, and C,
reducing the need for remote communication between services and improving runtime
performance.
Question 12
Refer to Exhibit.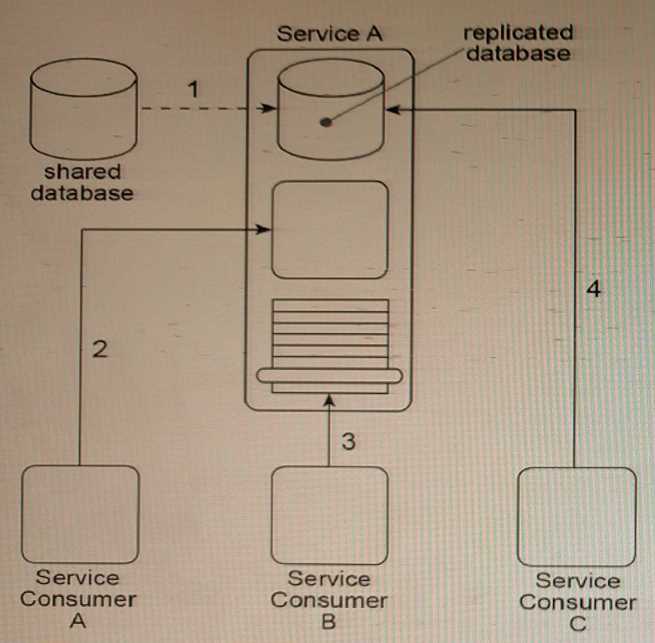
Service A is a utility service that provides generic data access logic to a database containing data that
is periodically replicated from a shared database (1). Because the Standardized Service Contract
principle was applied to the design of Service A, its service contract has been fully standardized.
The service architecture of Service A Is being accessed by three service consumers. Service Consumer
A accesses a component that is part of the Service A Implementation by Invoking it directly (2).
Service Consumer B invokes Service A by accessing Its service contract (3). Service Consumer C
directly accesses the replicated database that Is part of the Service A Implementation (4).
You've been told that the reason Service Consumers A and C bypass the published Service A service
contract is because, for security reasons, they are not allowed to access a subset of the capabilities in
the API that comprises the Service A service contract. How can the Service A architecture be changed
to enforce these security restrictions while avoiding negative forms of coupling?
- A. The Contract Centralization pattern can be applied to force all service consumers to access the Service A architecture via its published service contract. This will prevent negative forms of coupling that could lead to problems when the database is replaced. The Service Abstraction principle can then be applied to hide underlying service architecture details so that future service consumers cannot be designed to access any part of the underlying service implementation.
- B. The Contract Centralization pattern can be applied to force service consumers to access the Service A architecture via its published service contract only. The Service Loose Coupling principle can then be applied to ensure that the centralized service contract does not contain any content that is dependent on or derived from the underlying service implementation.
- C. The Contract Centralization pattern can be applied to force service consumers to access the Service A architecture via its published service contract only. The Concurrent Contracts pattern can be applied to Service A in order to establish one or more alternative service contracts. This allows service consumers with different levels of authorization to access different types of service logic via Service A's published service contracts.
- D. The Contract Centralization pattern can be applied to force service consumers to access the Service A architecture via its published service contract only. The Idempotent Capability pattern can be applied to Service A to establish alternative sets of service capabilities for service consumers with different levels of authorization.
Answer:
C
Explanation:
The Contract Centralization pattern can be applied to force service consumers to access the Service A
architecture via its published service contract only. The Service Loose Coupling principle can then be
applied to ensure that the centralized service contract does not contain any content that is
dependent on or derived from the underlying service implementation. This will enforce the security
restrictions while avoiding negative forms of coupling. By ensuring loose coupling, changes to the
implementation of Service A will not require changes to its published service contract, making it
easier to maintain and evolve the service.
Question 13
Refer to Exhibit.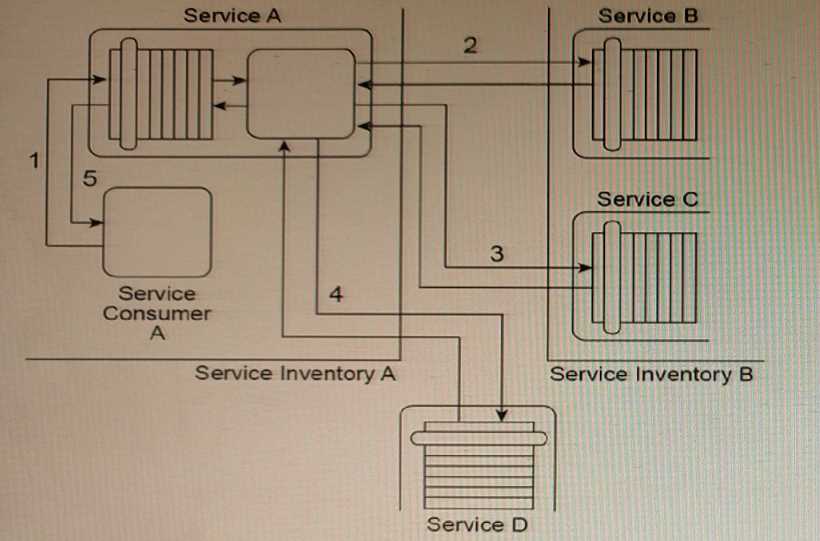
Service Consumer A and Service A reside in Service Inventory
- A. The Event-Driven Messaging pattern can be applied to establish a subscriber-publisher relationship between Service Consumer A and Service A. This gives Service A the flexibility to provide its response to Service Consumer A whenever it is able to collect the three data values without having to require that Service Consumer A remain stateful. The Asynchronous Queuing pattern can be applied to position a central messaging queue between Service A and Service B and between Service A and Service C. The Data Model Transformation and Protocol Bridging patterns can be applied to enable communication between Service A and Service B and between Service A and Service C. The Redundant Implementation pattern can be applied so that a copy of Service D is brought in-house and made part of Service Inventory A.
- B. The Asynchronous Queuing pattern can be applied to position a central messaging queue between Service A and Service B and between Service A and Service C and so that a separate messaging queue is positioned between Service A and Service Consumer A. The Data Model Transformation and Protocol Bridging patterns can be applied to enable communication between Service A and Service B and between Service A and Service C. The Redundant Implementation pattern can be applied so that a copy of Service D is brought in-house. The Legacy Wrapper pattern can be further applied to wrap Service D with a standardized service contract that is in compliance with the design standards used in Service Inventory A.
- C. The Containerization pattern can be applied to establish an environment for Service A to perform its processing autonomously. This gives Service A the flexibility to provide Service Consumer A with response messages consistently. The Asynchronous Queuing pattern can be applied so that a central messaging queue is positioned between Service A and Service B, between Service A and Service C, and between Service A and Service D. The Data Model Transformation and Protocol Bridging patterns can be applied to enable communication between Service A and Service B and between Service A and Service C.
- D. The Asynchronous Queuing pattern can be applied to position a message queue between Service A and Service B, between Service A and Service C, and between Service A and Service D. Additionally, a separate messaging queue is positioned between Service A and Service Consumer A. The Data Model Transformation and Protocol Bridging patterns can be applied to enable communication between Service A and Service B, between Service A and Service C, and between Service A and Service D. The Redundant Implementation pattern can be applied so that a copy of Service D is brought in-house. The Legacy Wrapper pattern can be further applied to wrap Service D with a standardized service contract that is in compliance with the design standards used in Service Inventory B.
Answer:
D
Explanation:
The Asynchronous Queuing pattern is applied to position a messaging queue between Service A,
Service B, Service C, Service D, and Service Consumer A. This ensures that messages can be passed
between these services without having to be in a stateful mode.
The Data Model Transformation and Protocol Bridging patterns are applied to enable communication
between Service A and Service B, Service A and Service C, and Service A and Service D, despite their
different data models and transport protocols.
The Redundant Implementation pattern is applied to bring a copy of Service D in-house to ensure
that it can be accessed locally and reduce the unpredictability of its performance.
The Legacy Wrapper pattern is applied to wrap Service D with a standardized service contract that
complies with the design standards used in Service Inventory B. This is useful for service consumers
who want to use Service D but do not want to change their existing applications or service contracts.
Overall, this approach provides a comprehensive solution that addresses the issues with Service A,
Service B, Service C, and Service D, while maintaining compliance with the Service Abstraction
principle.
Question 14
Refer to Exhibit.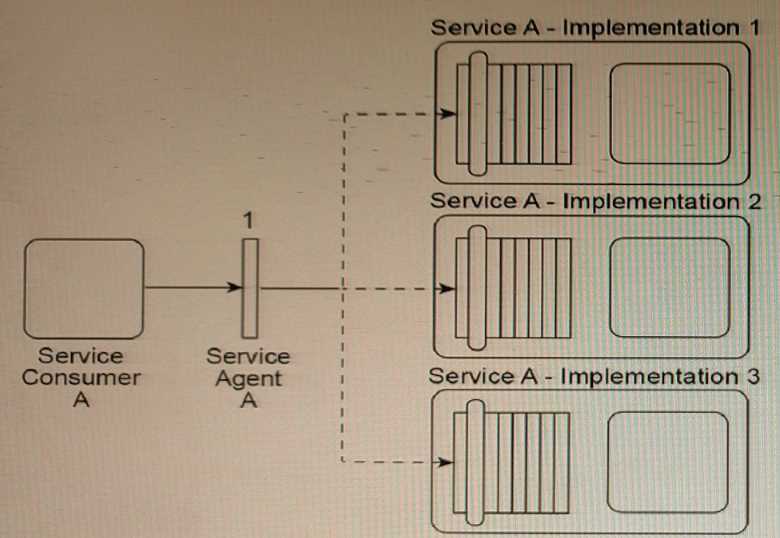
Service Consumer A sends a message to Service
- A. The Standardized Service Contract principle can be applied to ensure that the new service capability extends the existing service contract in a manner that is compliant with current design standards. The Redundant Implementation pattern can be applied to establish separate implementations of Service A that include duplicate databases with copies of the data that Service A requires from the shared database.
- B. The Service Autonomy principle can be applied to further isolate the individual implementations of Service A by separating them onto different physical servers. When the new service capability is added, the Service Data Replication pattern can be applied to give each implementation of Service A its own copy of the data it requires from the shared database.
- C. The Service Loose Coupling principle can be applied together with the Standardized Service Contract principle to ensure that Service Consumer A is not indirectly coupled to the shared database after the new service capability is added to the service contract. The Legacy Wrapper pattern can be applied to establish a new utility service that will provide standardized data access service capabilities for the shared database.
- D. The Service Autonomy principle can be applied to further isolate the individual implementations of Service A by separating them onto different physical servers. When the new service capability is added, the State Repository pattern can be applied to give each implementation of Service A its own copy of the data it requires from the shared database.
Answer:
B
Explanation:
By separating the individual implementations of Service A onto different physical servers, they can
be isolated from each other and from other clients and applications in the IT enterprise, which can
help improve performance. Additionally, using the Service Data Replication pattern to give each
implementation of Service A its own copy of the data it requires from the shared database can help
reduce the load on the shared database and improve performance. This can be especially important
when a new service capability is added that requires access to the shared database, as it can help
ensure that the performance of Service A is not impacted by the additional demands placed on the
shared database.
Question 15
Refer to Exhibit.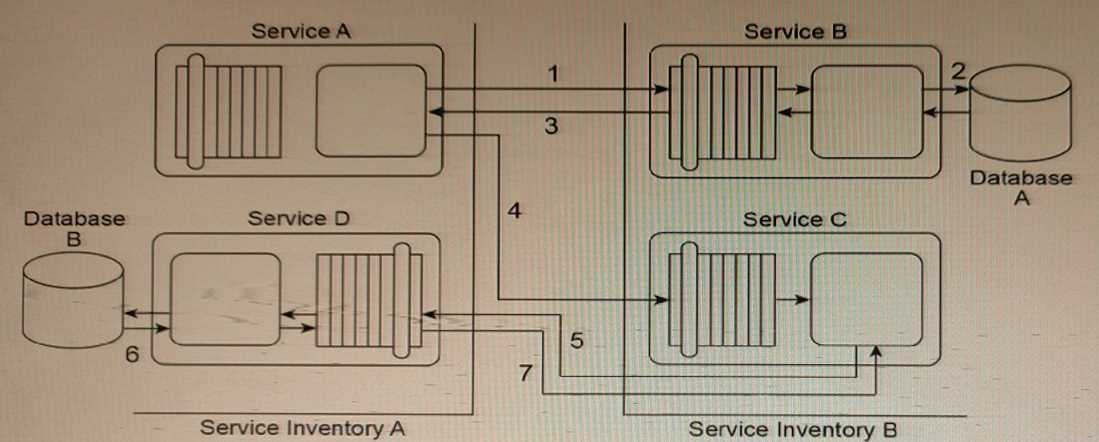
Service A sends a message to Service B (1). After Service B writes the message contents to Database
A (2), it issues a response message back to Service A (3). Service A then sends a message to Service C
(4). Upon receiving this message, Service C sends a message to Service D (5), which then writes the
message contents to Database B (6) and issues a response message back to Service C (7).
Service A and Service D are located in Service Inventory
- A. The Data Model Transformation pattern can be applied so that data model transformation logic is positioned between Service A and Service B, between Service C and Service D, and between the Service D logic and Database B. The Data Format Transformation pattern can be applied so that data format transformation logic is positioned between Service A and Service C, and between the Service B logic and Database A.
- B. The Protocol Bridging pattern can be applied so that protocol conversion logic is positioned between the Service B logic and Database A. The Data Format Transformation pattern can be applied so that data format transformation logic is positioned between Service A and Service B, between Service A and Service C, between Service C and Service D, and between the Service D logic and Database B.
- C. The Data Model Transformation pattern can be applied so that data model transformation logic is positioned between Service A and Service B, between Service A and Service C, between Service C and Service D, and between the Service D logic and Database B. The Data Format Transformation pattern can be applied so that data format transformation logic is positioned between the Service B logic and Database A.
- D. The Protocol Bridging pattern can be applied so that protocol conversion logic is positioned between Service A and Service B, between Service A and Service C, and between Service C and Service D. The Data Format Transformation pattern can be applied so that data format transformation logic is positioned between the Service B logic and Database A and between the Service D logic and Database B.
Answer:
C
Explanation:
This solution addresses the two main challenges in the service composition architecture: the
different XML schema used by services in Service Inventory A and Service Inventory B, and the
incompatible data formats of the two databases.
By applying the Data Model Transformation pattern, data model transformation logic can be inserted
to map the invoice-related data between the different XML schemas used by the services in Service
Inventory A and Service Inventory B. This can be done at the appropriate points in the message flow:
between Service A and Service B, between Service A and Service C, between Service C and Service D,
and between the Service D logic and Database B.
By applying the Data Format Transformation pattern, data format transformation logic can be
inserted to convert the XML-formatted data used by the services to the CSV format required by
Database A, and to convert the proprietary XML schema used by Database B to the XML schema used
by the services. This can be done between the Service B logic and Database A.
The Protocol Bridging pattern is not necessary in this case because all services are already
communicating using the same protocol (presumably HTTP or a similar protocol).